App for exploring and reporting on Vulnerability events.
| Author | Aplura, LLC |
| App Version | 1.2.4 |
| App Build | 13 |
| Creates an index | False |
| Implements summarization | No |
| Summary Indexing | False |
| Data Model Acceleration | If Enabled |
| Data Model | |
| Report Acceleration | False |
| Splunk Enterprise versions | 9.2, 9.1, 9.0 |
| Platforms | Splunk Enterprise, Splunk Cloud |
This App provides the following scripts:
Diag.py
For use with the diag command.
version.py
For use with keeping track of the version number within Python scripts.
This app provides Splunk dashboards, forms, and reports which can be used to explore your vulnerability events, and make sense of what can often be a large volume of data.
To do this, the app relies on the Splunk Common Information Model (CIM) for vulnerability events. This means that the app can report on any vulnerability data, as long as it has been on-boarded properly, and is available through the Vulnerabilities data model.
This app requires data model acceleration, which will use additional disk space. If you are using the Splunk App for Enterprise Security, this is already enabled, and should have been factored into your retention policies. If not, you should review the documentation on data model acceleration, how it uses disk space, and how to plan for it.
As mentioned above, the app uses the CIM for vulnerability events. The CIM allows you to take events from a number of sources or products, and report on them in one cohesive manner, using a common set of names for fields and event types.
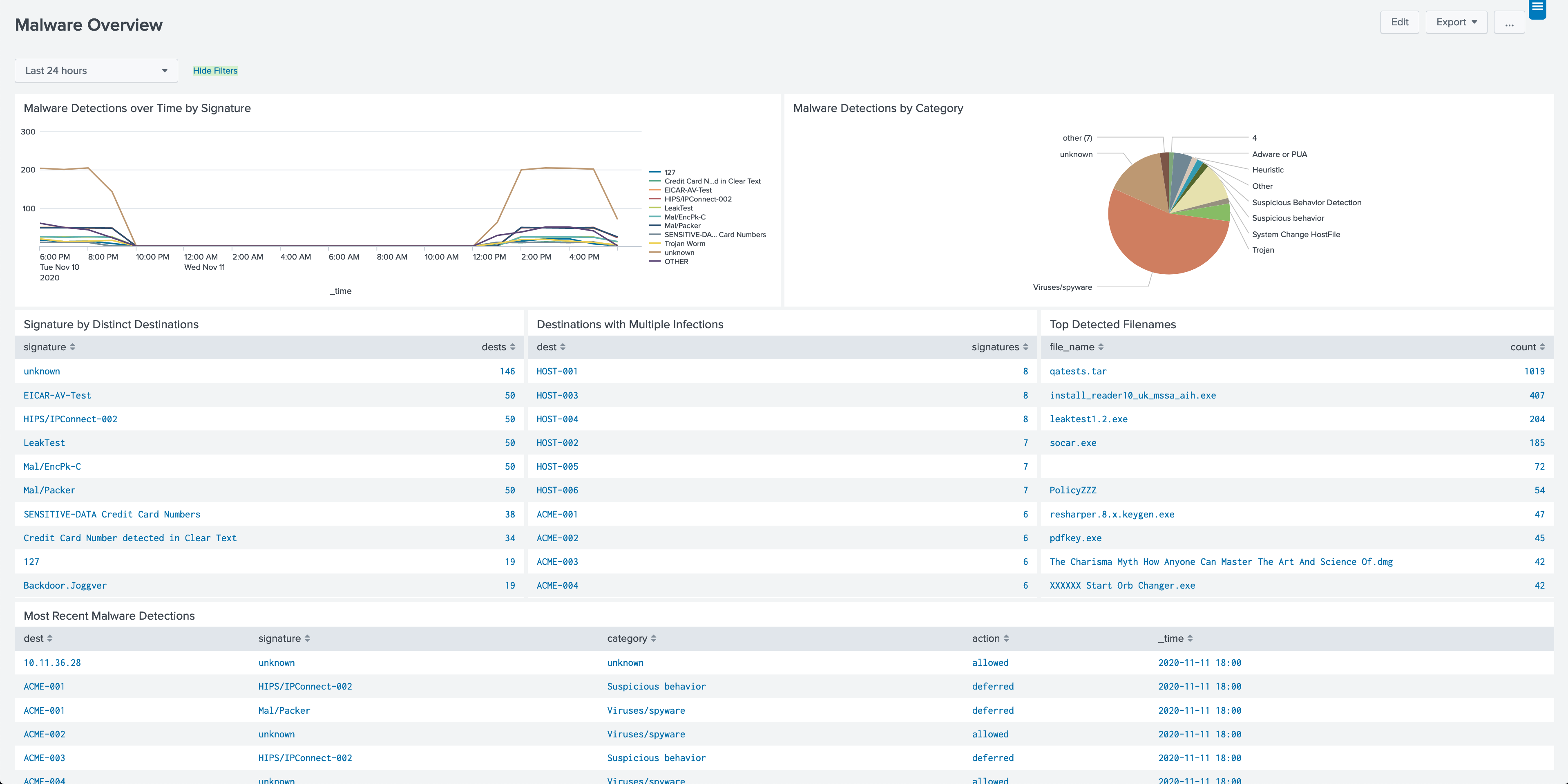
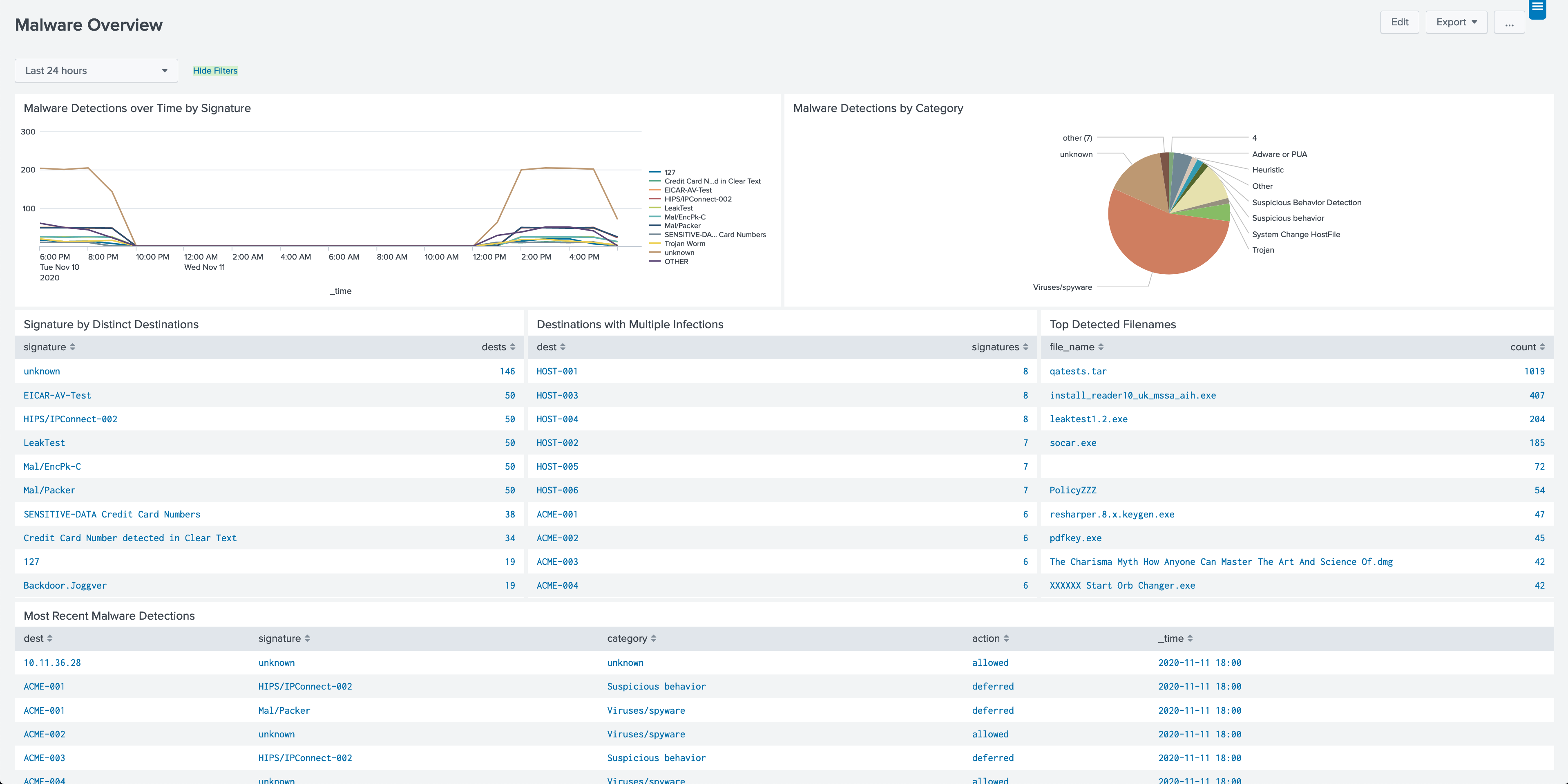
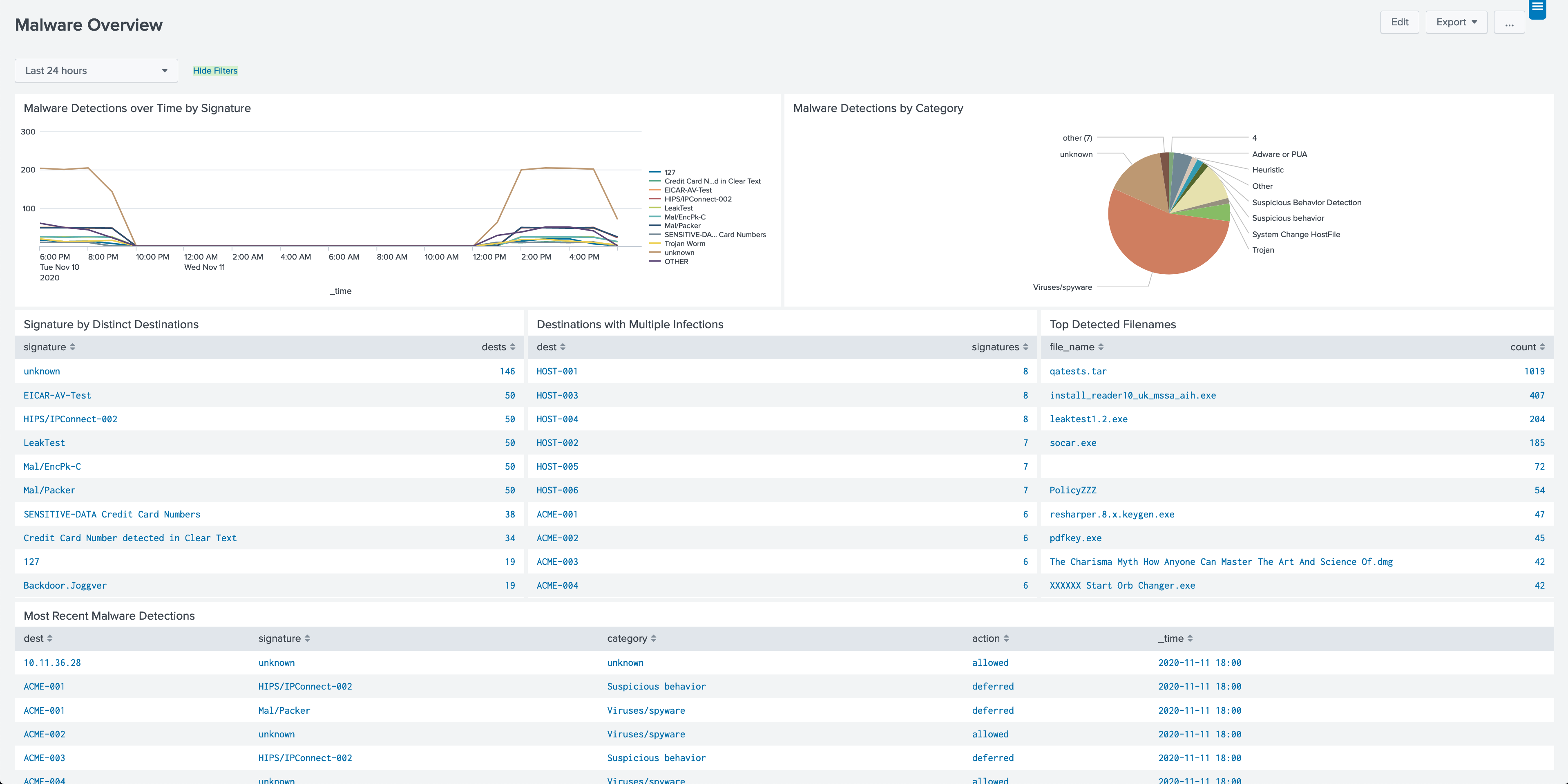
This dashboard serves as a jumping-off point for exploring your vulnerability data. It includes panels for vulnerabilities over time, severities, destinations, and signatures. Clicking on panels in this dashboard will drill down to the appropriate profile page for further exploration.
Form with reports and visualizations built around a set of severities (Critical, High, Medium, Low, Informational, Unknown, or all).
Form with reports and visualizations built around a destination (host or IP address, depending on how your CIM information for your vulnerability management events is mapped).
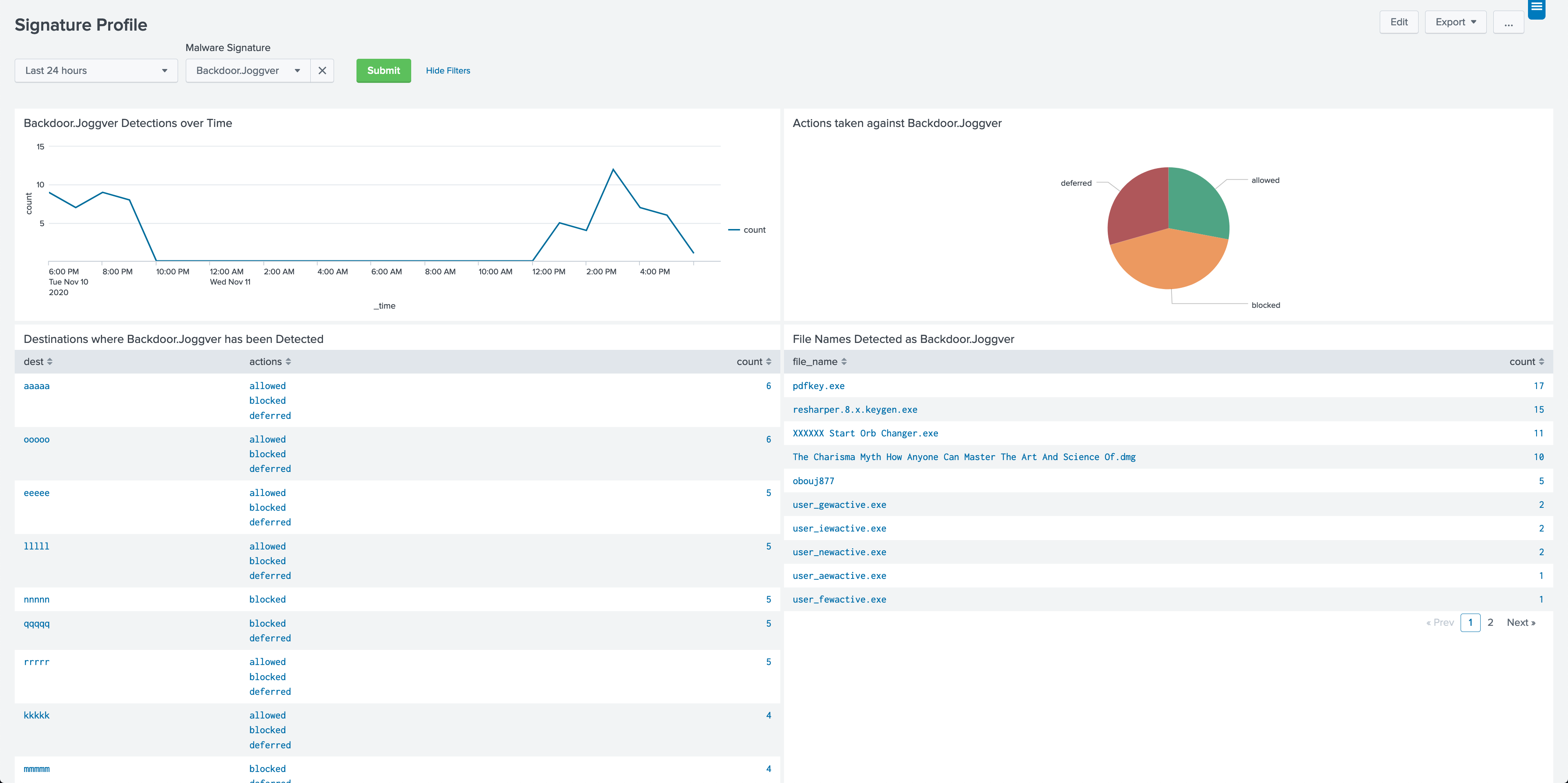
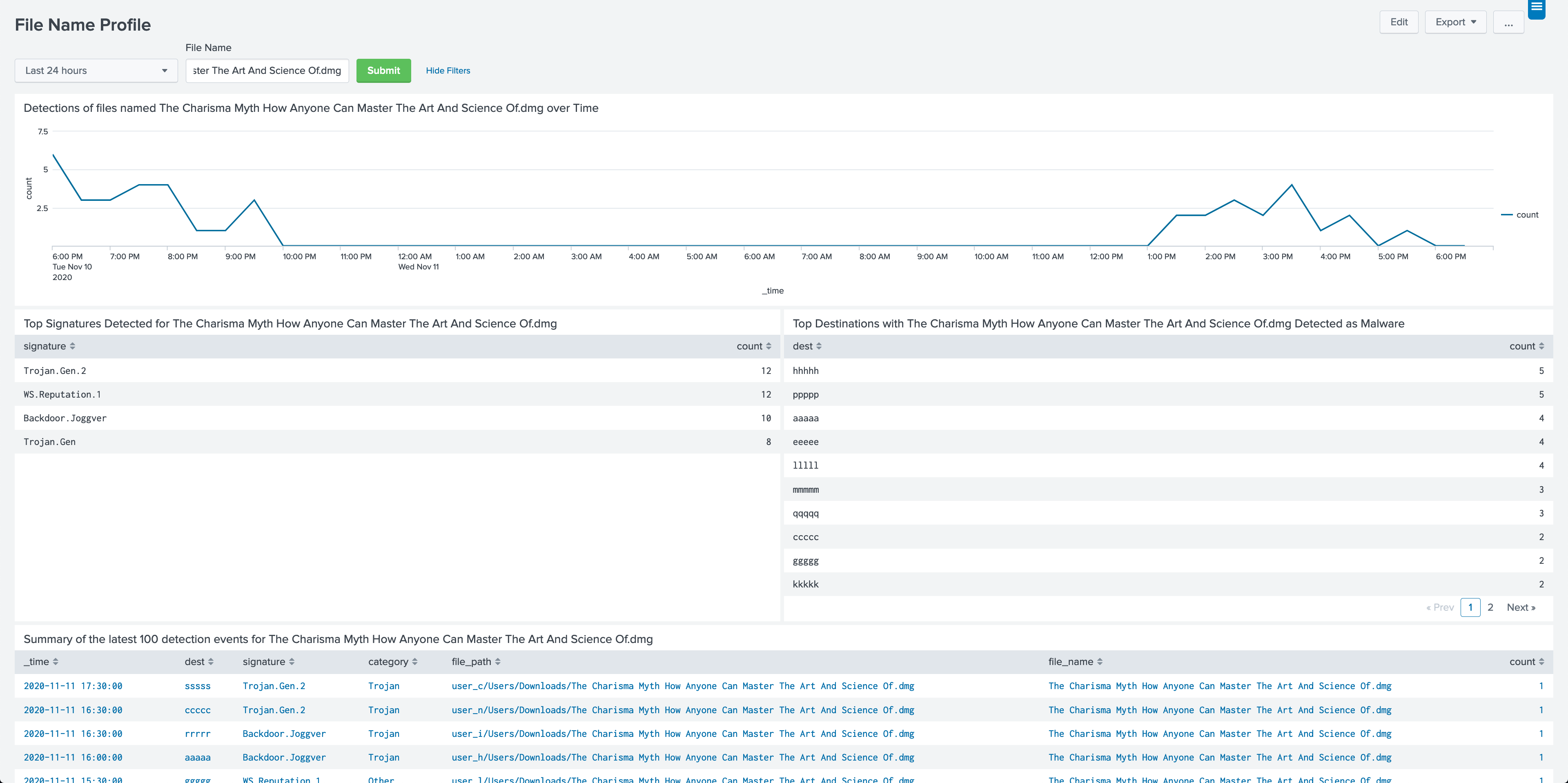
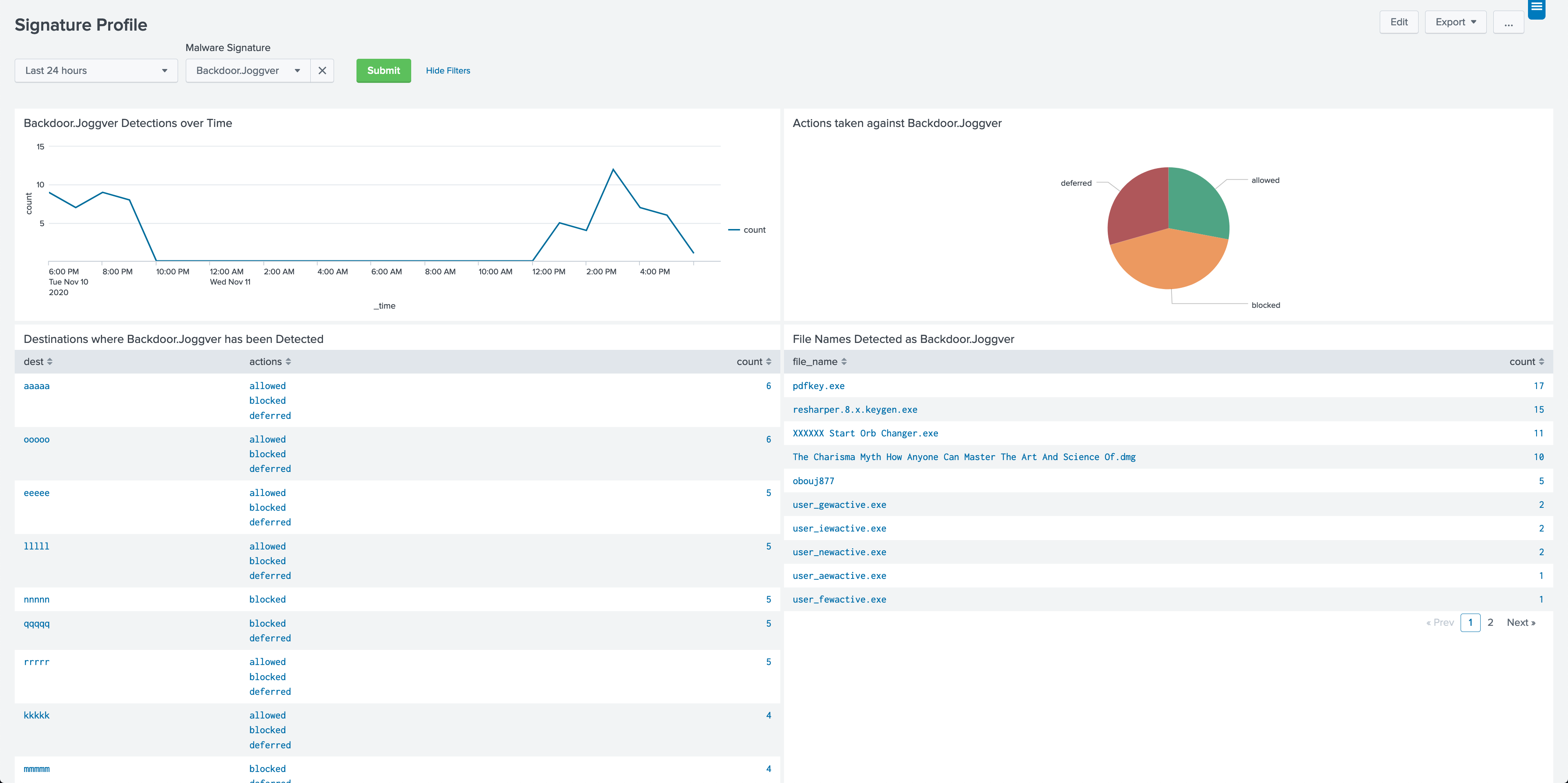
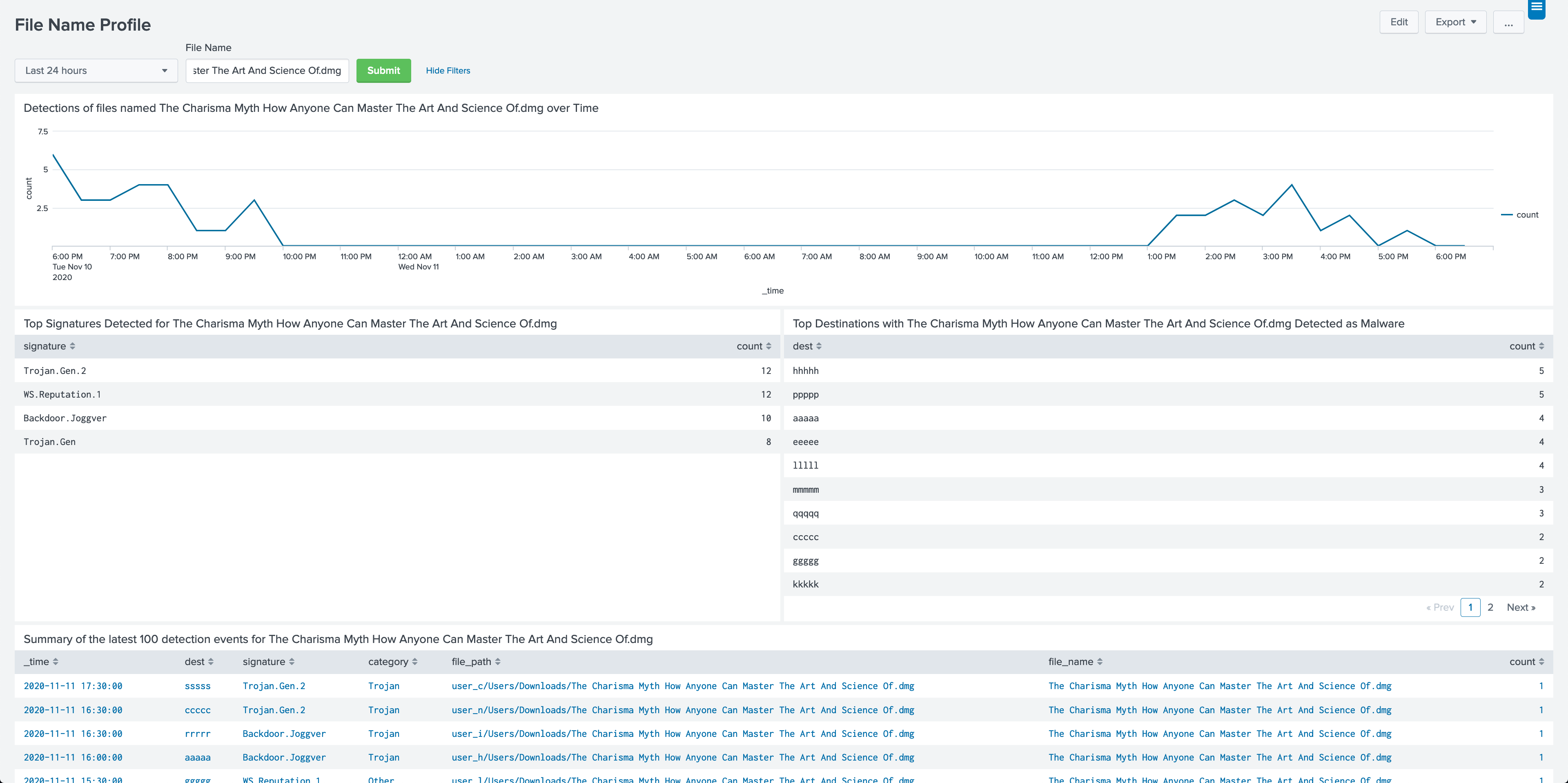
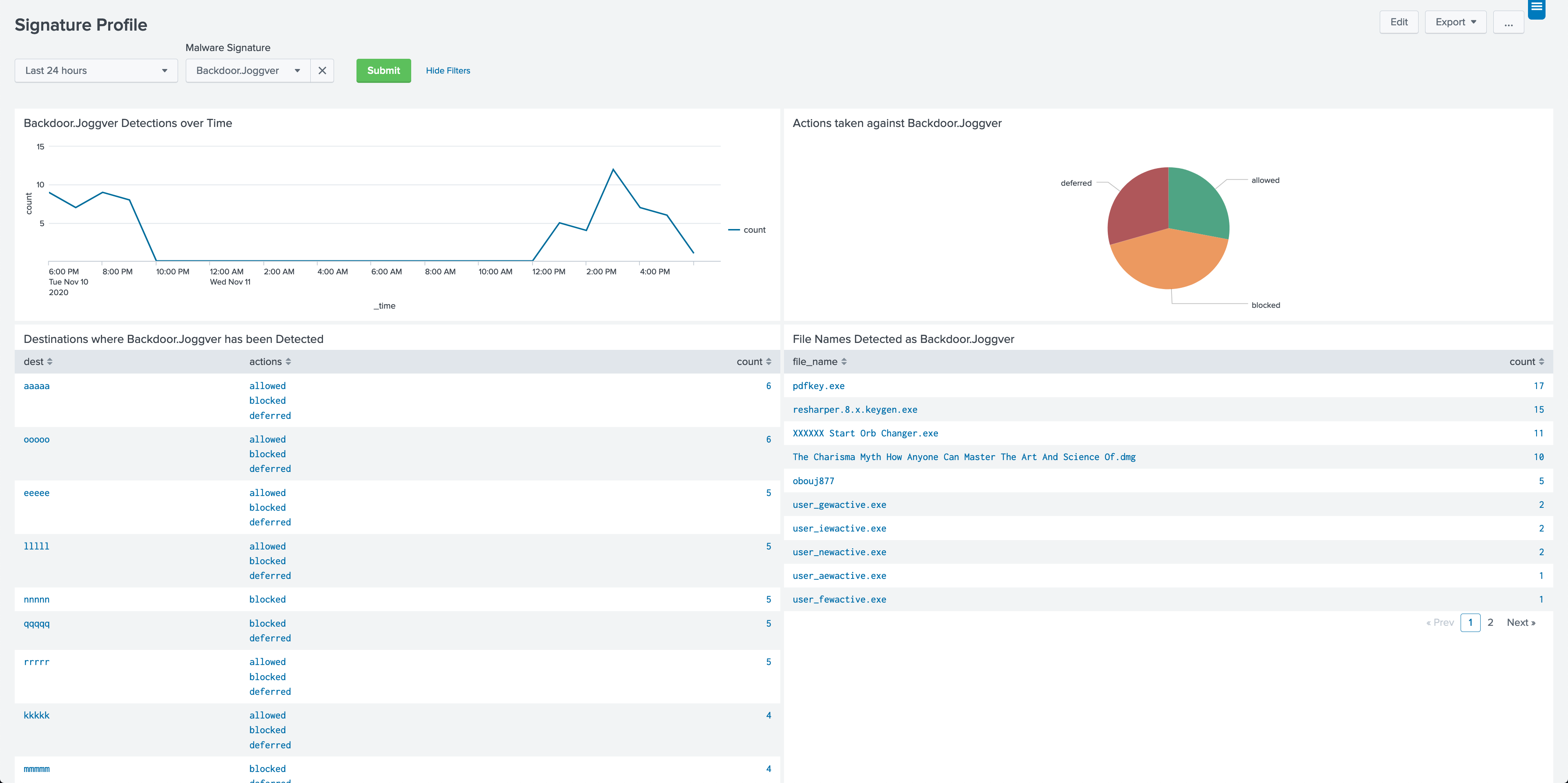
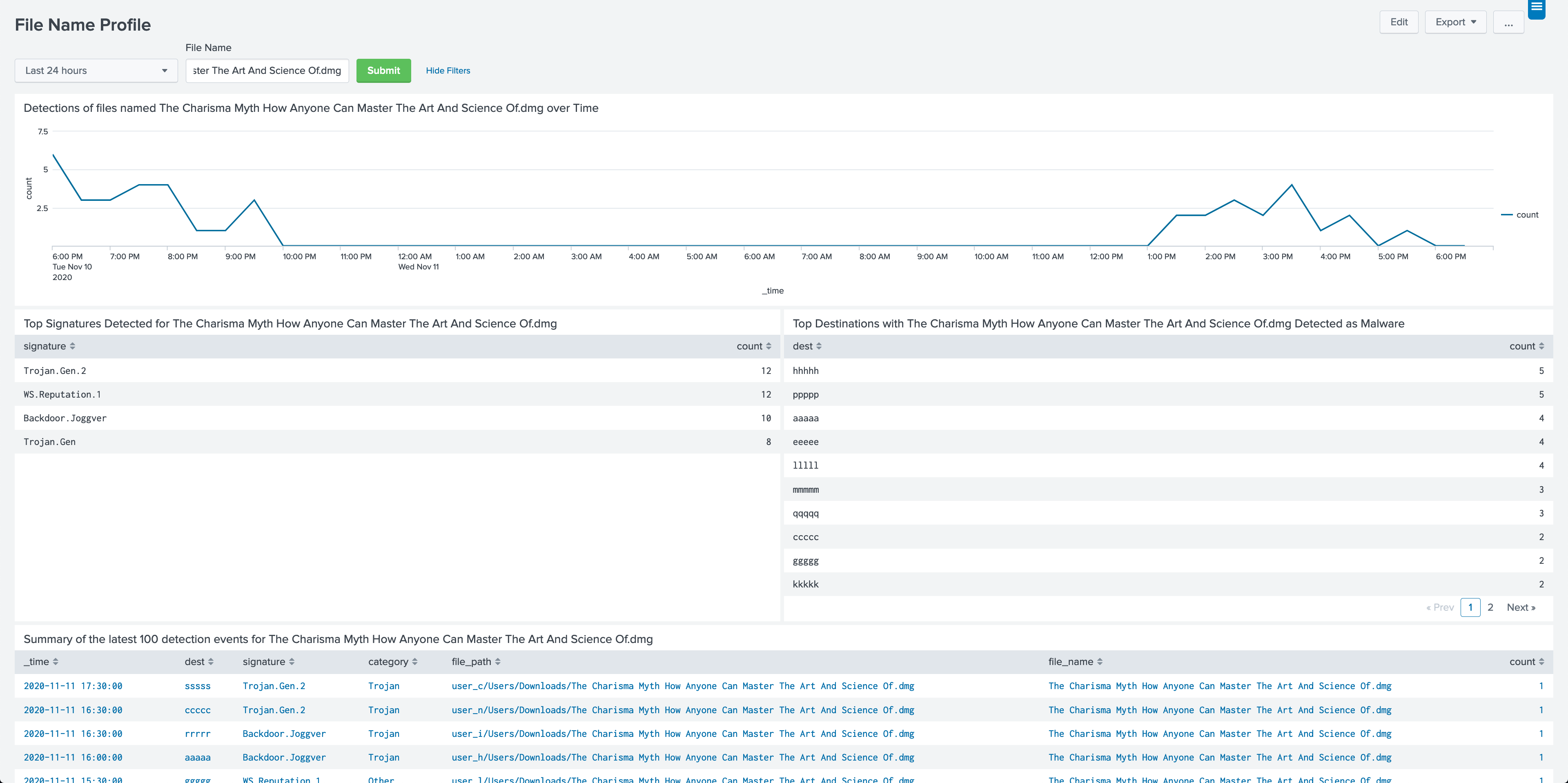
Form with reports and visualizations built around a signature, such as Terminal Services Encryption Level is Medium or Low or Buffer overrun in NT kernel message handling. Note that this is different than a CVE number, this is the text description of the vulnerability.
Form with many input variables. This is a flexible form designed to help generate a knockout list for fixing a set, or particular type of vulnerability.
Form for searching based on an identifier for a vulnerability, such as CVE, Cert, MSFT, or other reference number.
This dashboard provides panels to compare and contrast activity by sourcetypes. Use the time-picker to display sourcetype activity over time and to visualize event counts by sourcetype.
A simple HTML version of this document.
This app depends on data models included in the Splunk Common Information Model Add-on, specifically the {data_model} data model. Please review the information on configuring the acceleration on the data model.
The Splunk Common Information Model Add-on can be downloaded from Splunkbase.
This app has been tested with versions 4.9 of the CIM add-on.
In order to make the app respond and load quickly, accelerated data models are used to provide summary data. For this data to be available, the {data_model} data model must be accelerated. Information on how to enable acceleration for the {data_model} data model can be found here. The data model must be accelerated for the length of time for which you would like to see reporting.
Summary Indexing: No
Data Model Acceleration: If Enabled
Report Acceleration: No
PAVO Vulnerabilities App for Splunk contains the following lookup files.
PAVO Vulnerabilities App for Splunk does not include an event generator.
Compatibility with jQuery 3.5 and Splunk 8.x
Updated titles in dashboards
Documentation and Rename
Initial Release
As a Splunkbase app developer, you will have access to all Splunk development resources and receive a 10GB license to build an app that will help solve use cases for customers all over the world. Splunkbase has 1000+ apps from Splunk, our partners and our community. Find an app for most any data source and user need, or simply create your own with help from our developer portal.