Dashboards and reports on Malware events in Splunk.
| Author | Aplura, LLC |
| App Version | 1.0.4 |
| App Build | 18 |
| Creates an index | False |
| Implements summarization | No |
| Summary Indexing | False |
| Data Model Acceleration | If Enabled |
| Data Model | Malware |
| Report Acceleration | False |
| Splunk Enterprise versions | 9.2, 9.1, 9.0, 8.2, 8.1, 8.0 |
| Platforms | Splunk Enterprise, Splunk Cloud |
This App provides the following scripts:
Diag.py
For use with the diag command.
This app provides dashboards and reports based on events from anti-malware systems. To do this, the app relies on the Splunk Common Information Model (CIM) for malware detection events. This means that the app can report on any malware/av data, as long as it has been on-boarded properly, and is available through the Malware data model.
This app requires data model acceleration, which will use additional disk space. If you are using the Splunk App for Enterprise Security, this is already enabled, and should have been factored into your retention policies. If not, you should review the documentation on data model acceleration, how it uses disk space, and how to plan for it.
As mentioned above, the app uses the CIM for malware events. The CIM allows you to take events from a number of sources or products, and report on them in one cohesive manner, using a common set of names for fields and event types.
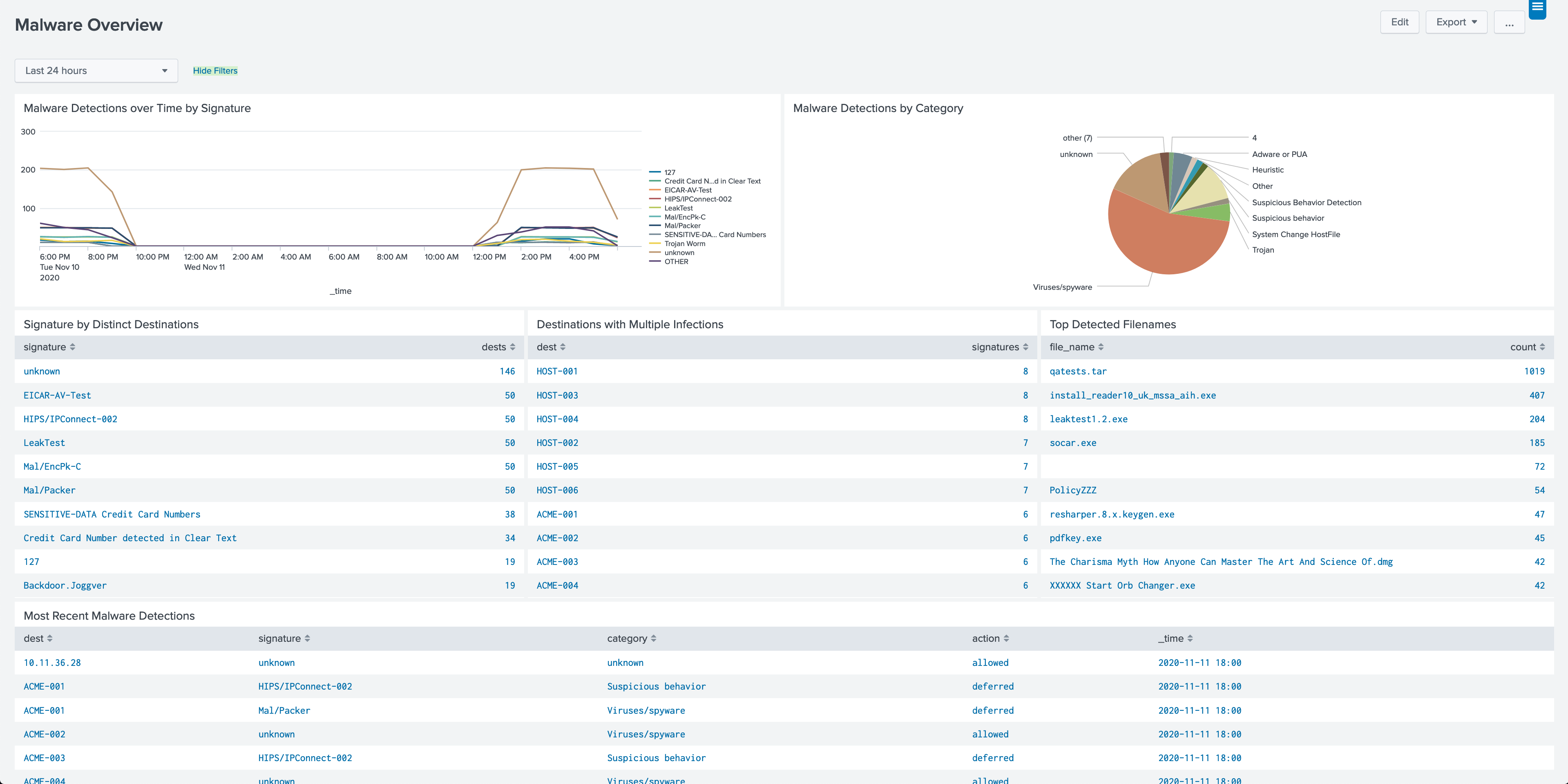
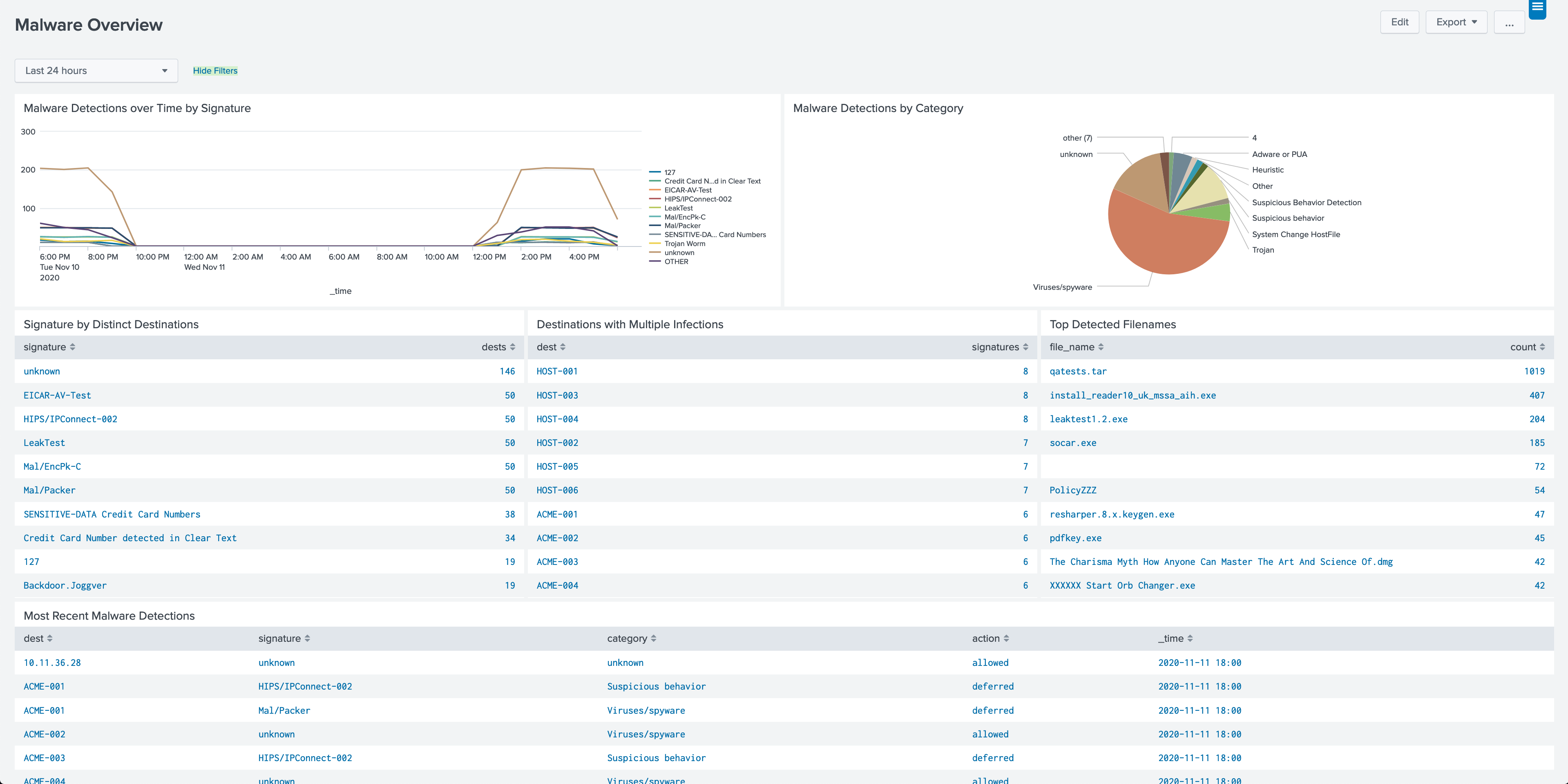
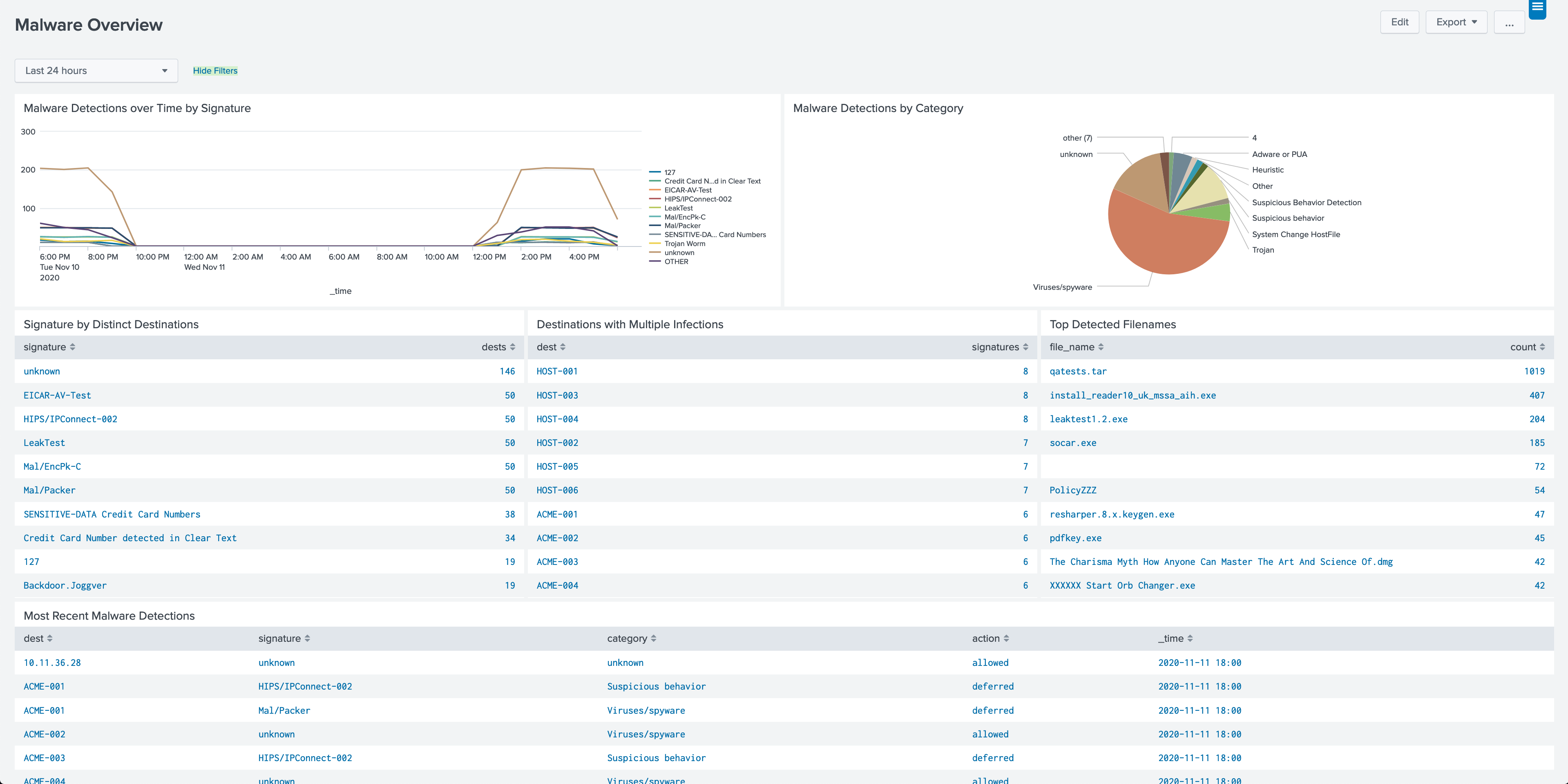
Provides a starting point for exploring your malware detection events. Most panels will drill-down to other pages in the application.
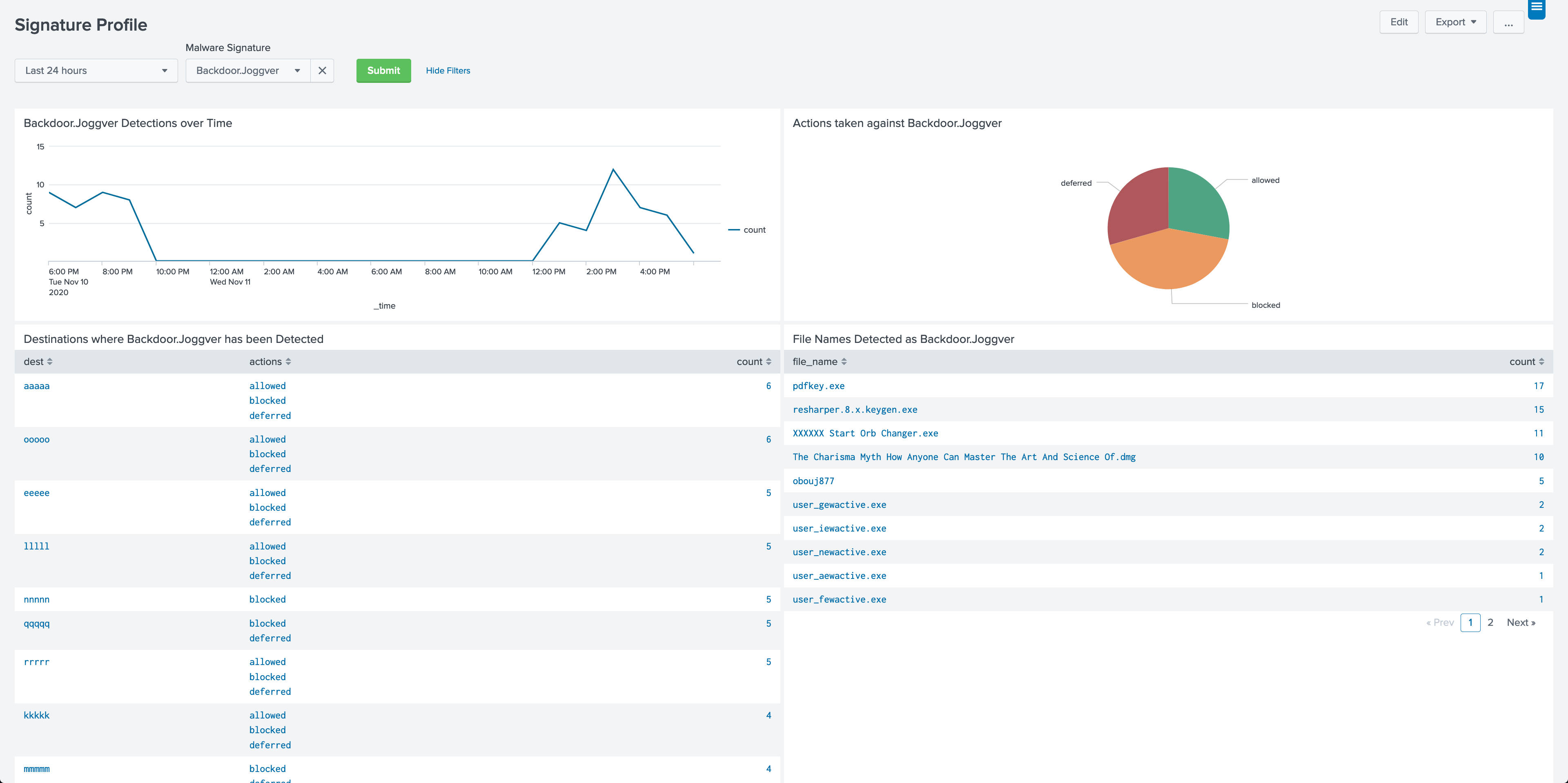
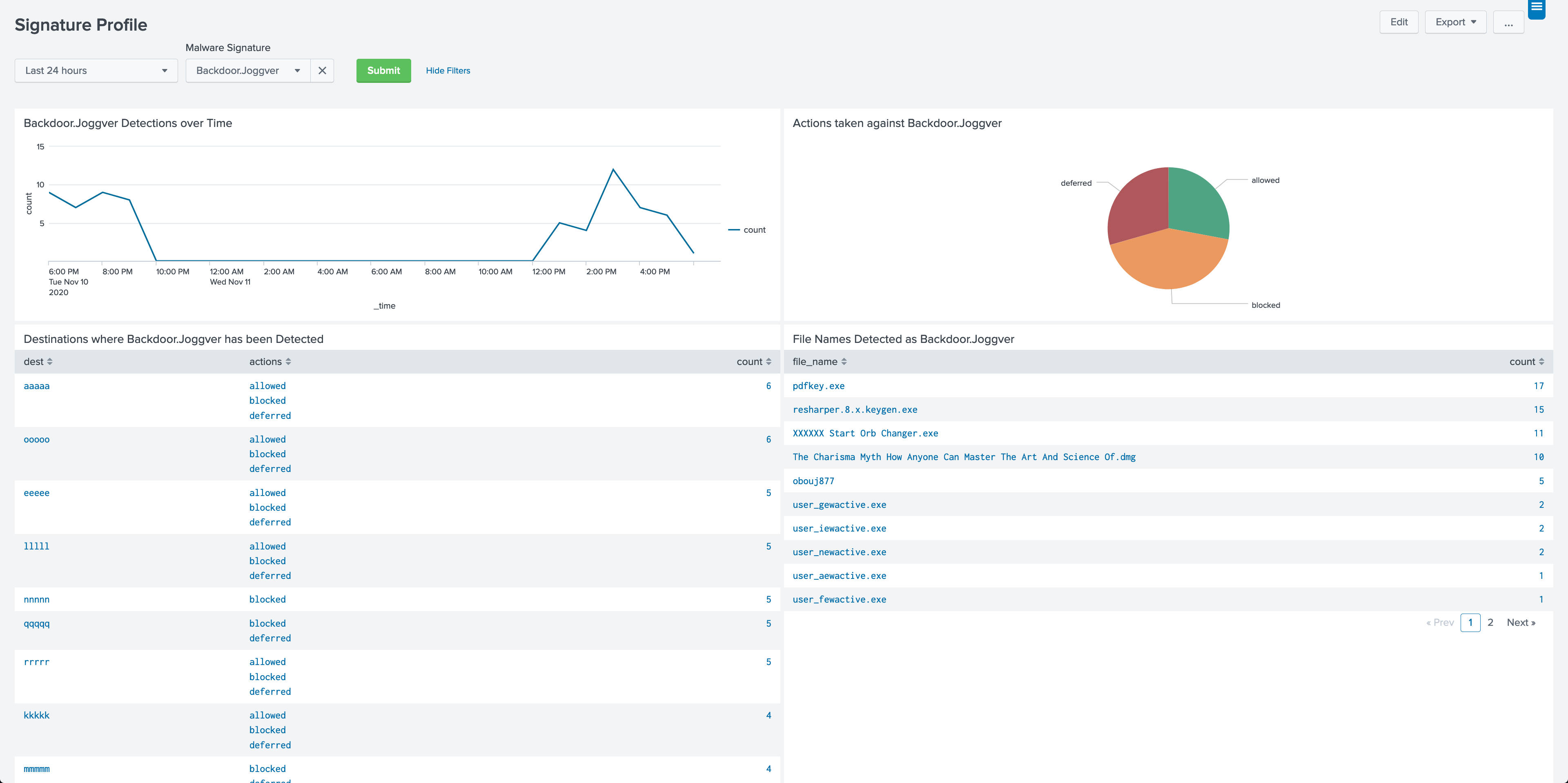
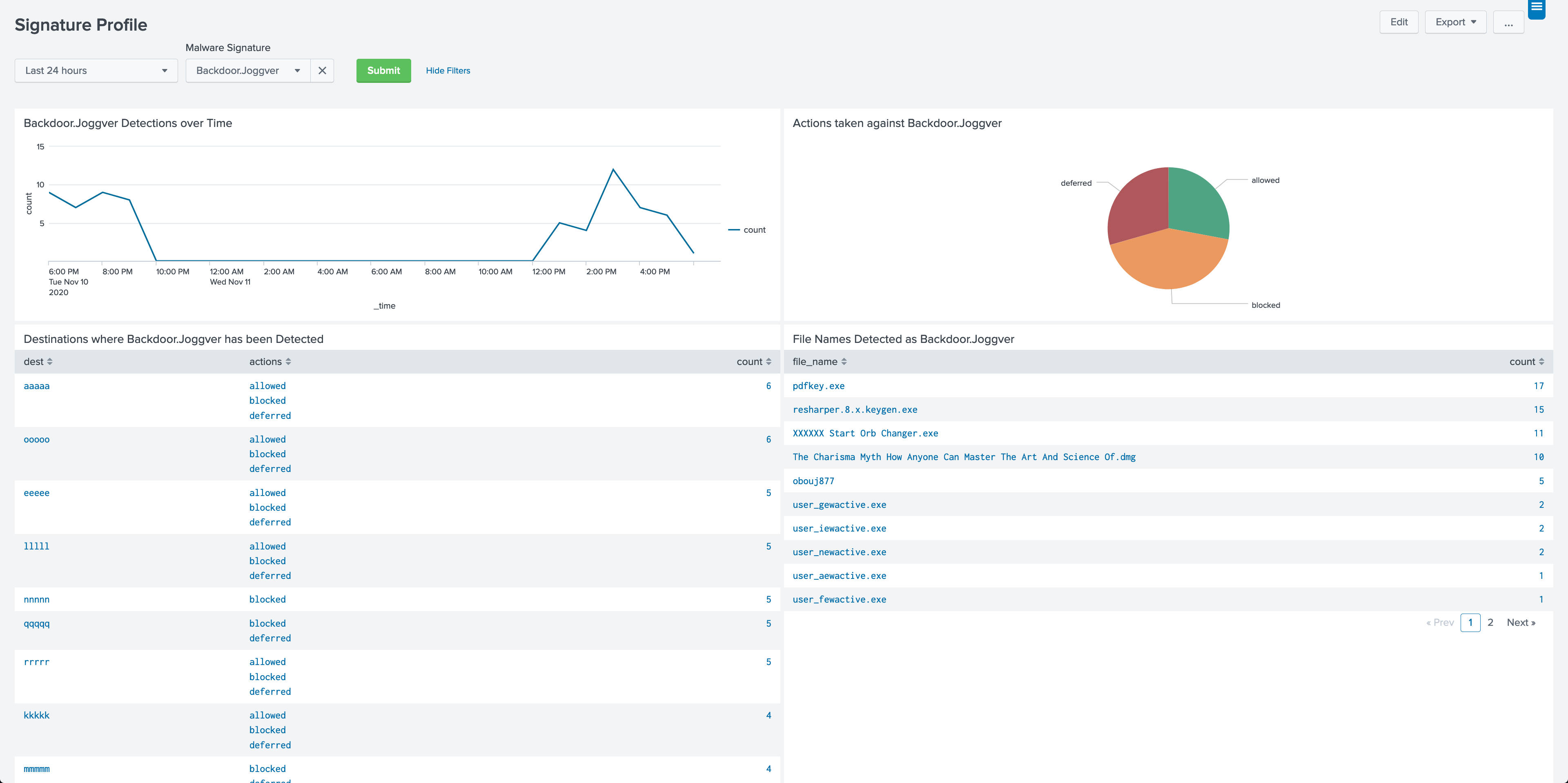
Panels around a particular signature detected. Note that there is no normalization for the values of this field, so this will be dependent on the naming used by the vendor for the individual anti-malware products.
Panels around a malware detected on a particular destination. The destination field in the Malware data model is the system on which the malware has been detected. This dashboard also contains a panel which shows malware operations (such as signatures being updated).
Panels with reports on category of malware. As with signature names, category names are not normalized across vendors.
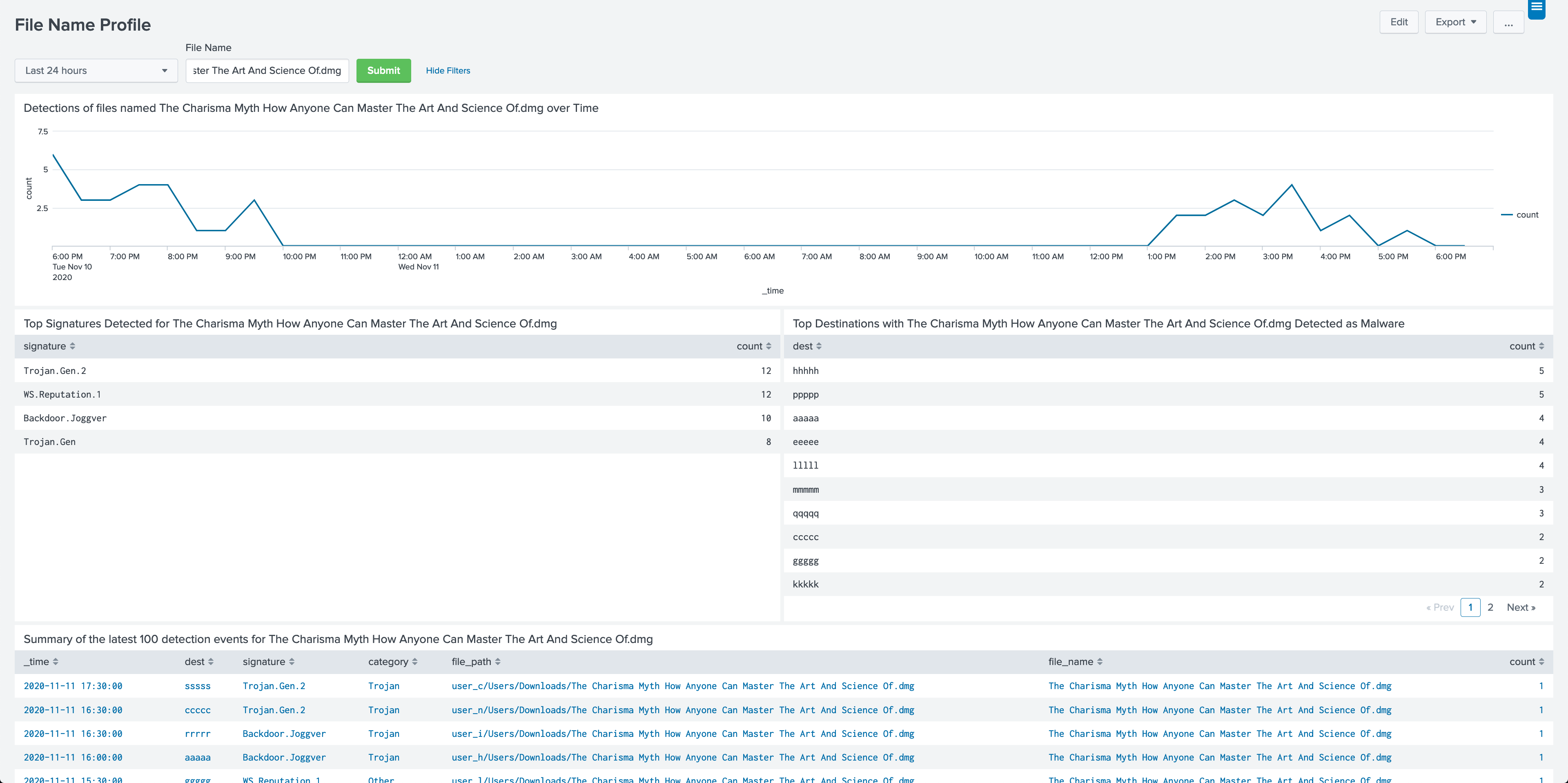
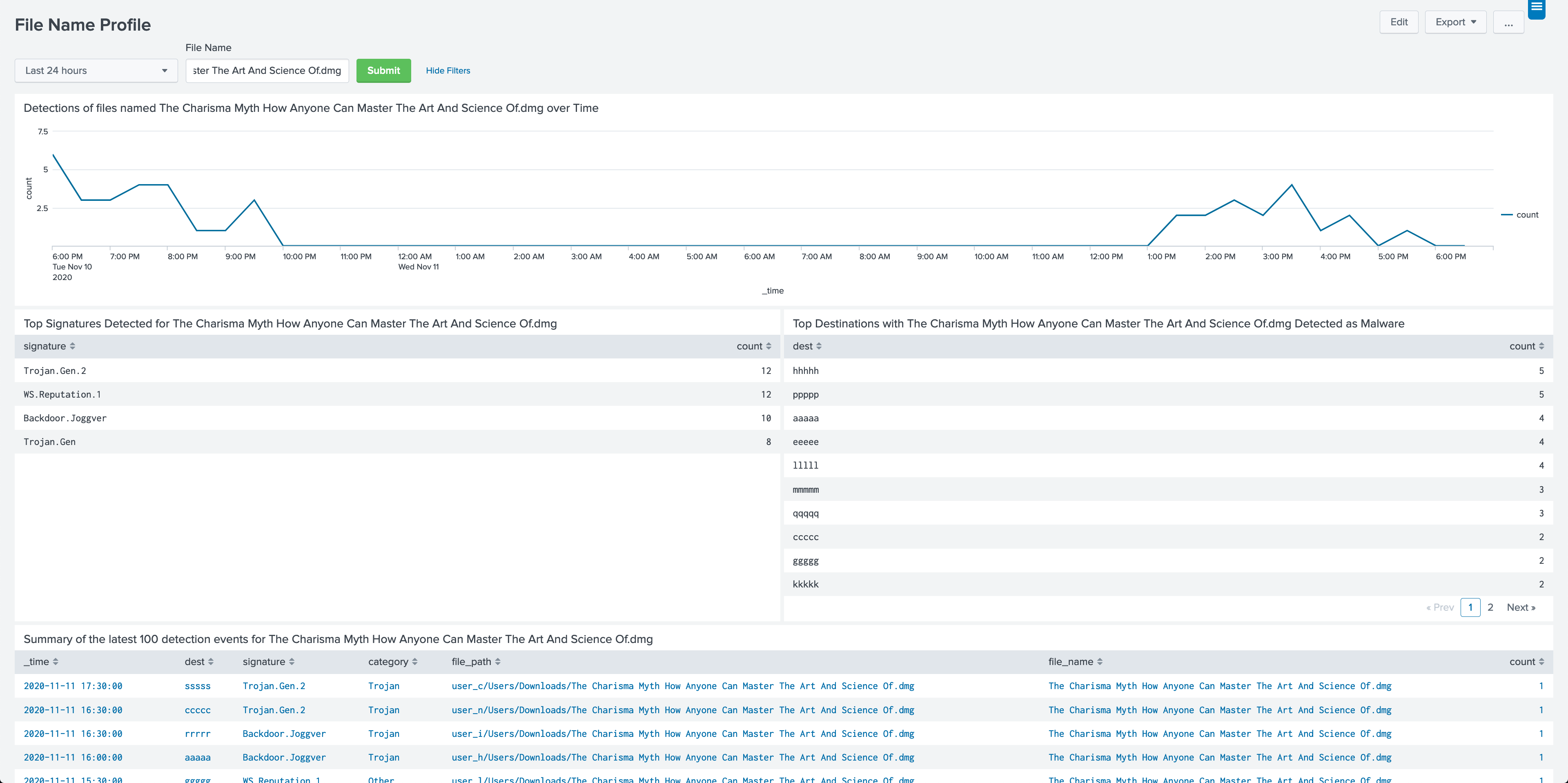
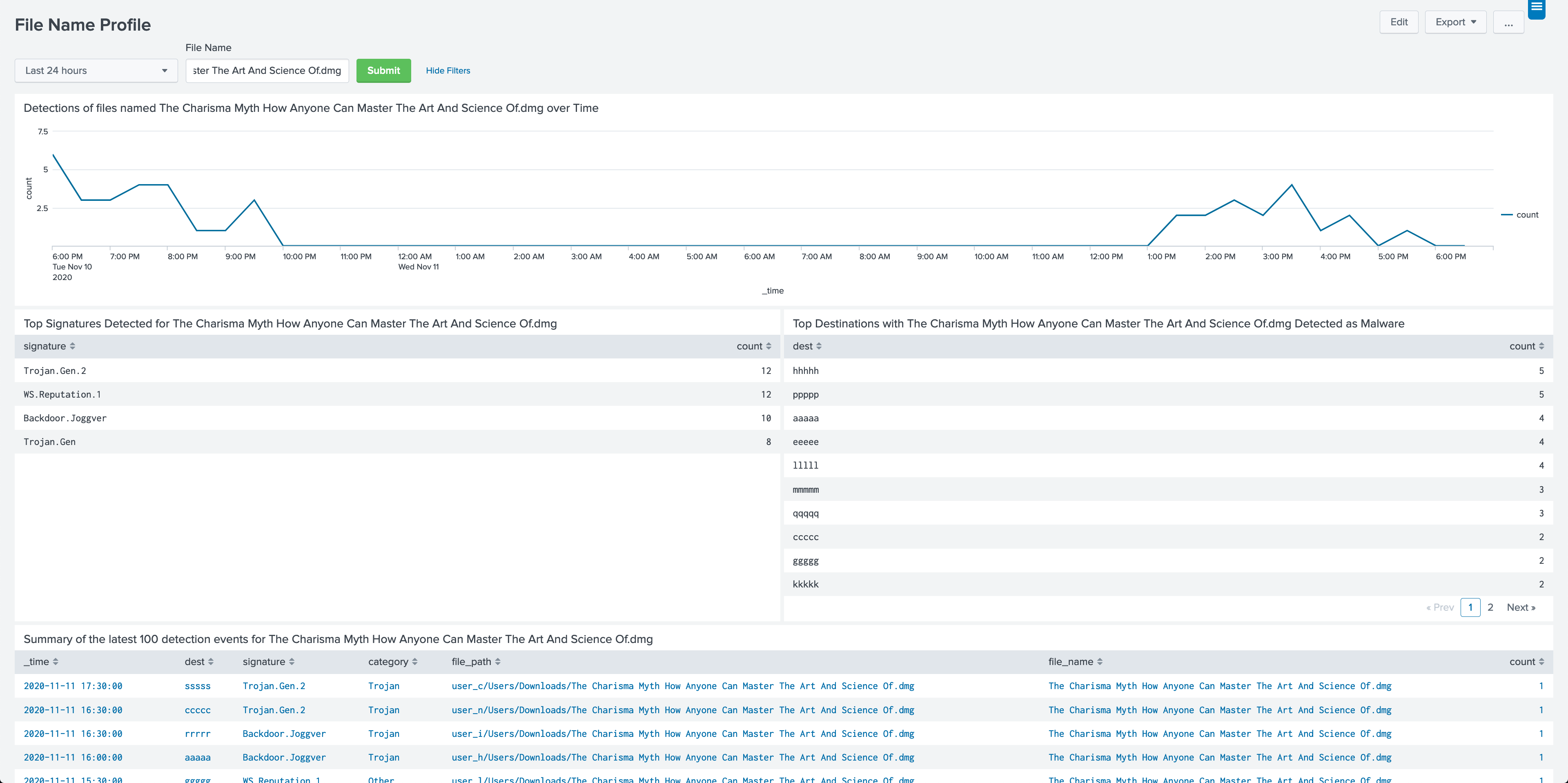
Reports on individual file names.
A form for finding events based on various field values.
Information about the sourcetypes which are present in the accelerated data.
A simple HTML version of this document.
Configure PAVO Malware App for Splunk
PAVO Malware App for Splunk contains the following lookup files.
PAVO Malware App for Splunk does not include an event generator.
Summary Indexing: No
Data Model Acceleration: If Enabled
Report Acceleration: No
Version 1.0.4 of
PAVO Malware App for Splunk has the following known issues:
Update dashboard titles
Documentation and Rename
Initial Release
As a Splunkbase app developer, you will have access to all Splunk development resources and receive a 10GB license to build an app that will help solve use cases for customers all over the world. Splunkbase has 1000+ apps from Splunk, our partners and our community. Find an app for most any data source and user need, or simply create your own with help from our developer portal.