


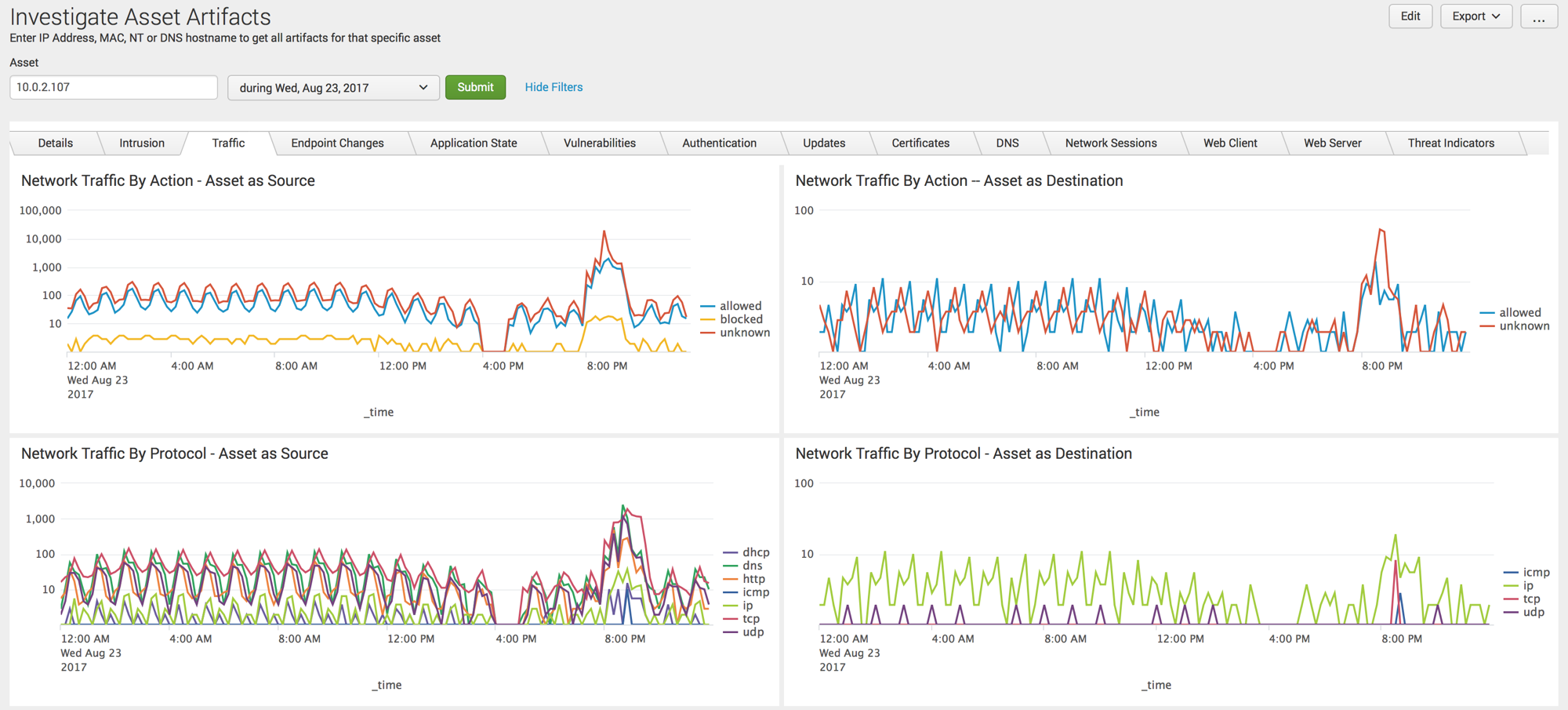



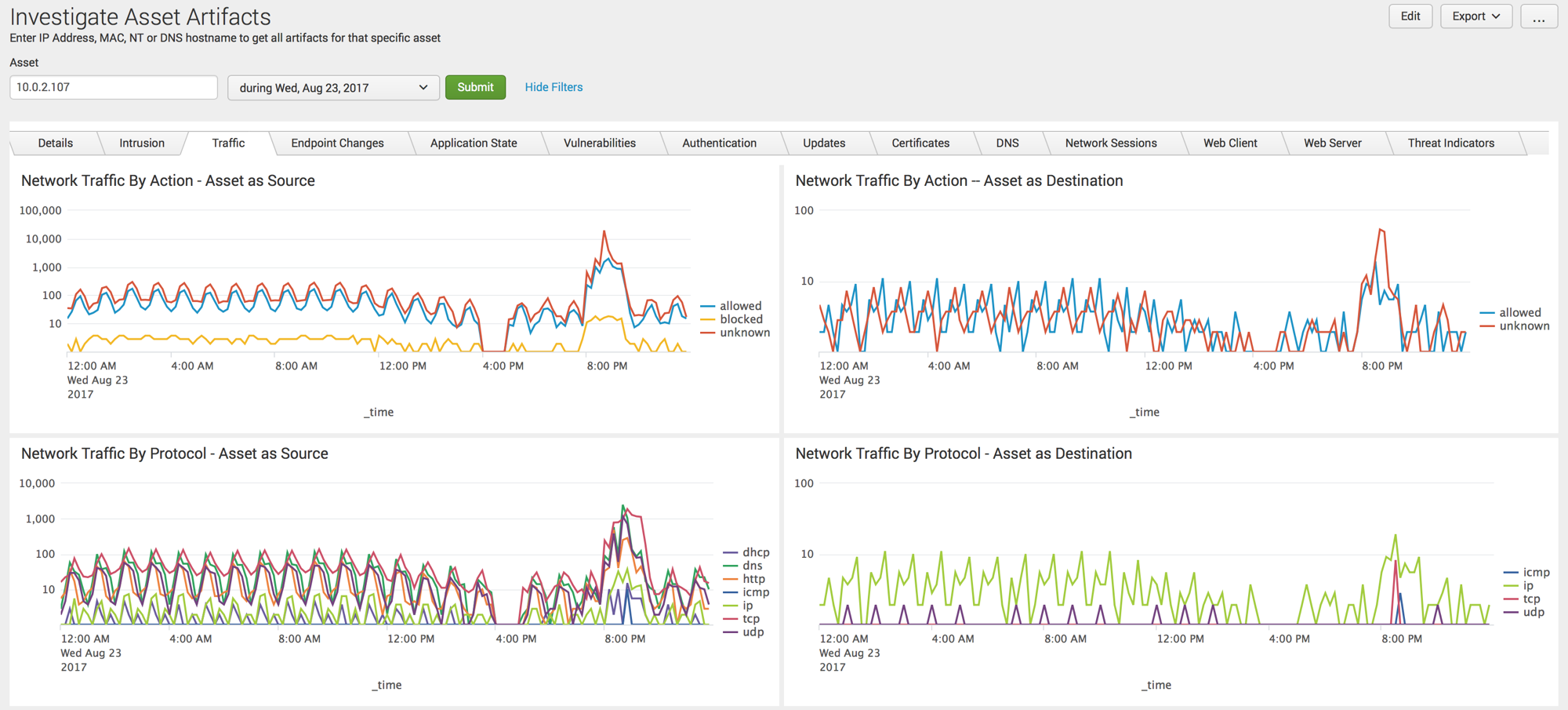



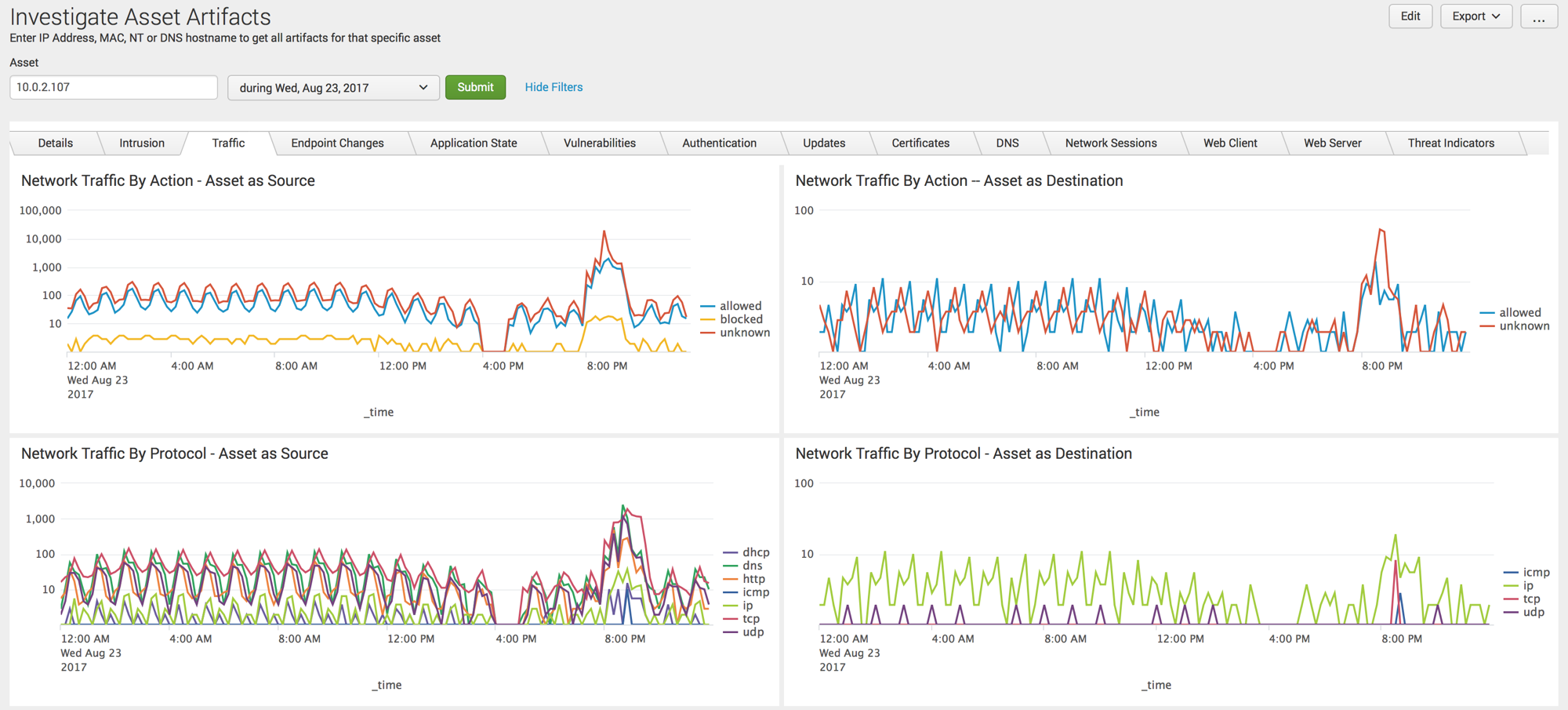
SA-Investigator is an extension built to integrate with Splunk Enterprise Security. It provides a set of views based on the asset, identity or file/process. Rather than searching all data for the asset you are looking for, target your investigation on the asset(s) or identity of interest and then pivot to authentication events or network traffic events that are pertinent to the asset(s) or identity under investigation.
URL Toolbox https://splunkbase.splunk.com/app/2734/ is required for searches to populate a few of the panels within the DNS and Web tabs.
The Alexa (transitioning to the Cisco Umbrella 1M) list is also leveraged but if you are installing with Enterprise Security this will be available.
Enterprise Security is assumed to be installed due to workflow actions and certain drill-downs will take users to Enterprise Security dashboards.
SA-Investigator does not require population of Asset & Identity Framework to work. However, if multiple values (IP Address, MAC, NT Hostname, Hostname) for assets are stored within ES, all values will be searched when using the asset investigator.
-Updated the Risk tab to better support RBA use cases
-Removed broken Endpoint dashboard panels
-Added text/checkbox filters to many tabular panels to filter search results including Endpoint, Authentication, DNS, Web and Certificates
-Added drilldowns to tabular endpoint panels that pivot to the identity investigator when user is clicked on, asset investigator when src or dest is clicked on, file/process investigator when process_exec, process_name or parent_process_exec is clicked on.
-Added parent process panel to file/process dashboard under endpoint with filters for dest and user as well as a pivot on the process_name for better search-ability of spawned processes.
-Added drilldowns to numerous panels that previously didn't with specific cell drilldowns that are called out in the search panel
-Added SSL Certificate detail panels
-Added additional authentication fields to Authentication by User for more context
-Modified file hash search to use Endpoint DM
-Removed glass table button on all screens as this has been deprecated in ES 6.6.x and later - currently commented out.
-Misc Bug Fixes
-Updated dashboards for jQuery 3.5 support
-Added support for RenderXML=1 in Windows Event and Sysmon TAs
-Added wildcard support for file hash panels to be more forgiving for TAs that concatenate multiple hashes into a single hash field
-Update threat intel searches to accommodate new threat generating searches introduced in ES 6.4
-Update 4688 Process Command Line and Account Name fields to accommodate changes in Windows TA.
-Revised hunting indicators dashboard to include more datamodels
-Misc bug fixes
-Added a dashboard for hunting indicators historically. Initial datamodels used are Email, Network Resolution, Network Traffic and Endpoint.Processes. This is an initial foray and will continue to expand in future releases.
-Fixed drill-downs for Endpoint tab to provide greater specificity
-Improved asset search to improve ease of use and increase performance
-Improved file name and file hash searches
-Fixed an issue where the tabs in javascript weren't loading with version 7.3.3 and newer
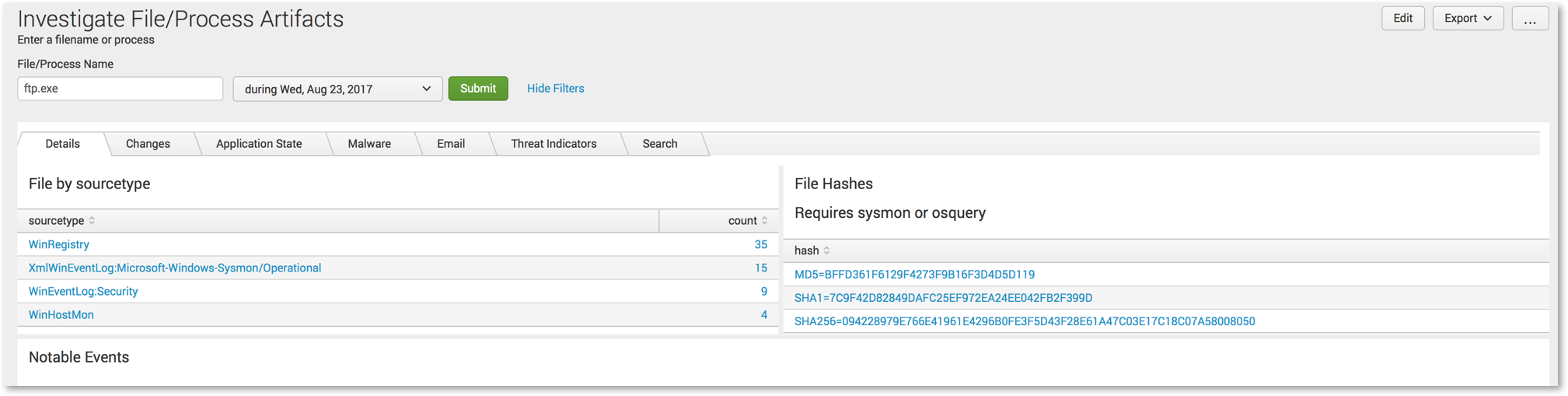
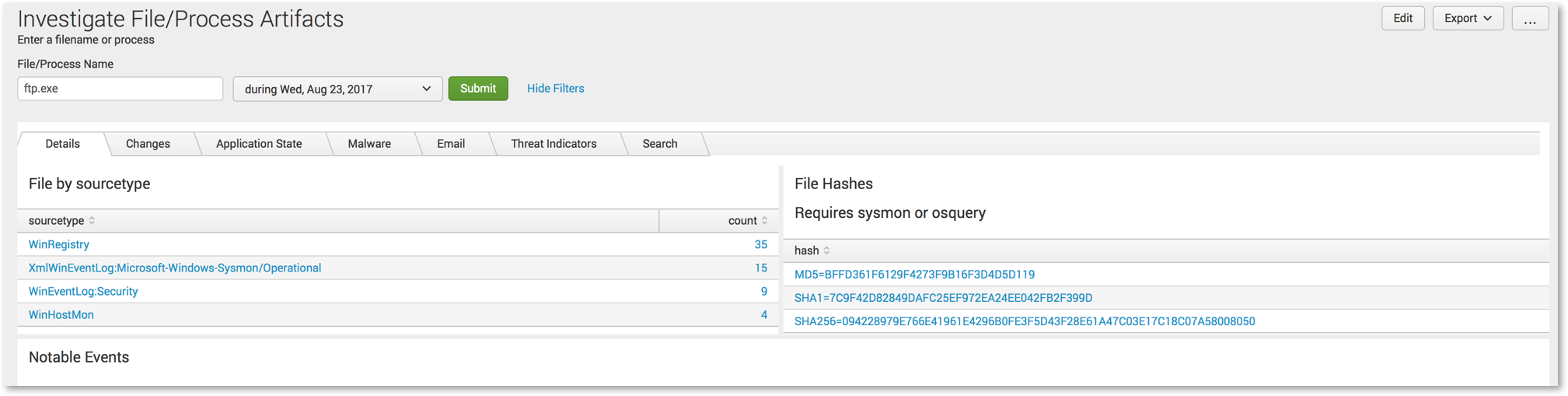
-Added drill down from File/Process Artifacts to Hash Artifacts
-Added drill down from Asset Artifacts on Network Traffic IPs associated with host to better facilitate searches where no IP exists in Asset table
-Added additional filters on File/Process Artifacts view
-Added workflow actions to pivot to file/process and hashes from Incident Review
-Fixed File/Process Artifacts drill down - Endpoint - Application State Process Details
-Fixed Sysmon search in hashes to drill down on EventCode 1
-Fixed Network Traffic by App panel to strip out file paths to enable drill downs
-Added custom messages on each pane when no results are found so that it is immediately apparent that no data is found.
-Added spinning wheel icon so that users have better awareness that searches are still in progress.
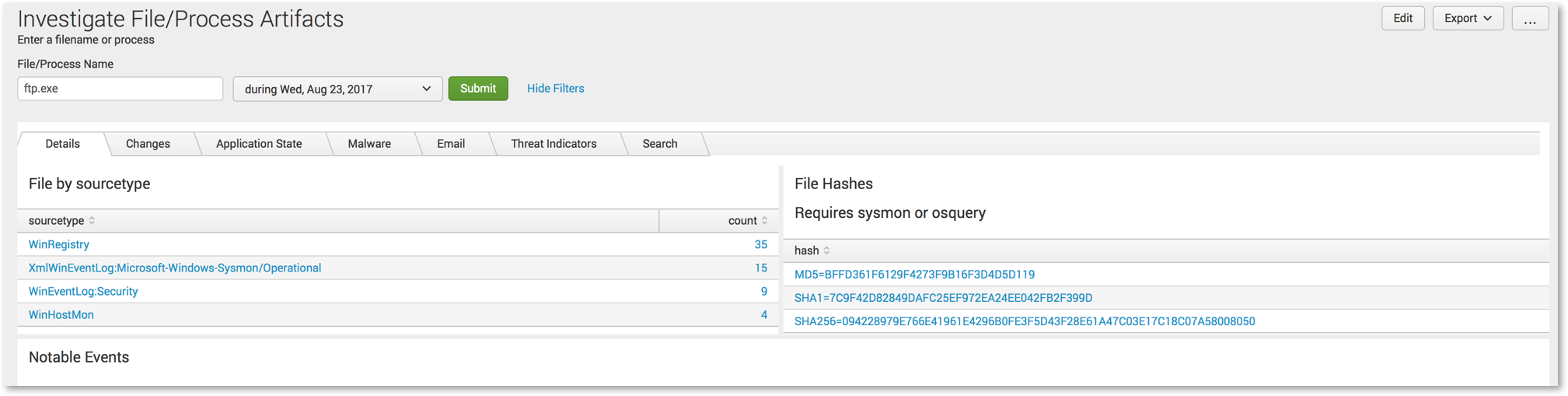
-Initial release of the Hash Artifact dashboard so that a hash can be entered in and searched across different data models much like assets, identities and file names.
-Users will need to add the hash artifacts dashboard view to the ES navigation
-The primary focus of this release was improving speed of search. This version has been tested against 100K assets and 60K user accounts for query performance. The biggest change is the elimination of the subsearches in the panels while retaining the ability to search asset and identity framework values like IP, DNS, NT Hostname and MAC in the case of assets and multiple identities.
-Added new panels and tabs for the Endpoint and Change datamodels (requires CIM 4.12)
-Commented out the Change Analysis and Application State datamodels as they are deprecated with 4.12 - Note that they can be re-enabled if desired.
-Modified identity search to autopopulate escape characters for usernames with a format of domain\username
-Modified the Windows Event Search tab to search specific fields for assets (host,dvc,src and dest) and identity (user) and added the ability to search multiple Windows Event Codes concurrently (comma separated)
-Modified the sourcetype search to search specific fields for assets (host,dvc,src and dest) and identity (user)
-Modified the search panel to generate a multiselect list of sourcetypes to choose from and then search specific fields for assets (host,dvc,src and dest) and identity (user)
-Updated drill-down searches to accomodate refined searches and eliminate subsearches wherever possible
-Added additional drill-down searches and pivots to other ES or SA-Investigator dashboards
-Removed individual time pickers for threat and dns panels
-Removed multi-asset search
-Added multi-select index search to file investigator
-Added multi-select index search tabs to asset and identity investigator
-Added drill down in Application State Details for raw data for file investigator
-Improved search formatting and output of OSQuery and Sysmon hashes at process creation and added drilldown to events
-Added Web tab to file investigator
-Added Windows Event 4688 Search tab for file investigator
-Added Windows Event Search tab in asset and identity investigators to search against 1:many indexes and a single event code
-Added panels to the asset detail tab that show the likely IP addresses of a hostname based on network traffic information (if applicable). This can be useful if a host name is in the asset table but it does not have a specific IP address mapped to it.
-All tablular results should sort oldest to newest
-Added note reminding everyone to use \ as an escape character for domain\user notation
-Fixed drilldowns for multi-asset searches
-Fixed search associated with DNS and Alexa-1M
-Misc drilldown searches were improved and cleaned up
-Add Risk Tab to both Asset and Identity and calculate All Time, 30 and 7 Day scores as well as detail and charting.
-Add html link for glass table network topology to be easily added to both asset and identity (requires editing the simple XML for the URL of the glass table)
-Added Search Tab to both Asset and Identity which allows sourcetype counts and full search of all events regardless of the field that the asset value(s) are stored in NOTE-this search can be very expensive if run over a very long time so these have their own time pickers to allow users to pick a specific time frame to search for this data
-Fixed notable event fields not fully populating
-Fixed asset searches to use macro instead of datamodel command to improve search
-Fixed labels to ensure better look and feel with Splunk's new visualization libraries
-Fixed a few line charts that were not formatted correctly
-Added exclusion lists for Windows Events, domains, services, processes and ports
-Enhance searches in Threat Indicator Tab
-Added multiple asset search capability
-Improved content in endpoint changes tab
-Initial Release
-Added text/checkbox filters to many tabular panels to filter search results including Endpoint, Authentication, DNS, Web and Certificates
-Added drilldowns to tabular endpoint panels that pivot to the identity investigator when user is clicked on, asset investigator when src or dest is clicked on, file/process investigator when process_exec, process_name or parent_process_exec is clicked on.
-Added parent process panel to file/process dashboard under endpoint with filters for dest and user as well as a pivot on the process_name for better search-ability of spawned processes.
-Added drilldowns to numerous panels that previously didn't with specific cell drilldowns that are called out in the search panel
-Added SSL Certificate detail panels
-Added additional authentication fields to Authentication by User for more context
-Modified file hash search to use Endpoint DM
-Removed glass table button on all screens as this has been deprecated in ES 6.6.x and later - currently commented out.
-Misc Bug Fixes
-Added missing jQuery version attribute for Cloud Compliance
-Change to default.meta for app import settings
-Updated dashboards for jQuery 3.5 support
-Added support for RenderXML=1 in Windows Event and Sysmon TAs
-Added wildcard support for file hash panels to be more forgiving for TAs that concatenate multiple hashes into a single hash field
-Update threat intel searches to accommodate new threat generating searches introduced in ES 6.4
-Update 4688 Process Command Line and Account Name fields to accommodate changes in Windows TA.
-Revised hunting indicators dashboard to include more datamodels
-Misc bug fixes
-Added a dashboard for hunting indicators historically. Initial datamodels used are Email, Network Resolution, Network Traffic and Endpoint.Processes. This is an initial foray and will continue to expand in future releases.
-Fixed drill-downs for Endpoint tab to provide greater specificity
-Improved asset search to improve ease of use and increase performance
-Improved file name and file hash searches
-Updated javascript to fix tabs not loading (Special thanks to Patrick Bland & Egan Davson for their assistance)
-Added drill down from File/Process Artifacts to Hash Artifacts
-Added drill down from Asset Artifacts on Network Traffic IPs associated with host to better facilitate searches where no IP exists in Asset table
-Added additional filters on File/Process Artifacts view
This release adds custom messages on each pane when no results are found so that it is immediately apparent that no data is found. A spinning wheel icon is also added particularly for non-TSTATS searches so that the user has better awareness that searches are still in progress. An initial release of a new dashboard, Hash Artifacts is included as well so that a hash can be entered in and searches across different data models much like assets, identities and file names. Finally there are a few bug fixes to address some issues that have been identified. Users will need to add the hash artifacts dashboard view to the ES navigation.
As a Splunkbase app developer, you will have access to all Splunk development resources and receive a 10GB license to build an app that will help solve use cases for customers all over the world. Splunkbase has 1000+ apps from Splunk, our partners and our community. Find an app for most any data source and user need, or simply create your own with help from our developer portal.