











The Windows Event Log Analysis Splunk App assumes that Splunk is collecting information from Windows servers and workstation via the Universal Forwarder, the local Windows event log collector or remotely via WMI.
It analyzes the entries from indexes matching the "index="wineventlog" OR source=WinEventLog" criteria. This matches the defaults used by the Universal Forwarder, the collection of local Windows event logs and the collection via WMI.
To collect the logs from remote computers without installing the Universal Forwarded on each computer, configure the forwarding of event logs to central location using the Windows built-in event forwarding.
The Interesting Processes section from the Processes dashboard is partially based on a presentation by Michael Gough from www.malwarearchaeology.com: "The Top 10 Windows Event ID's Used To Catch Hackers In The Act". See https://www.malwarearchaeology.com/home/2016/5/7/windows-top-10-event-logs-from-my-dell-enterprise-security-summit-talk for the presentation slides and information on how to enable the auditing of processes, including command-line based ones. The list of “interesting processes” is based on a study by JPCERT CC (Japan Computer Emergency Response Team Coordination Center) on detecting lateral movement through tracking of event logs (https://www.jpcert.or.jp/english/pub/sr/ir_research.html). The list is stored in C:\Program Files\Splunk\etc\apps\eventid\lookups\interesting_processes.csv and it can be adjusted with a text editor if needed.
If not data is displayed, please verify that the Universal Forwarder is installed properly and that the all the Windows event logs are sent to the "wineventlog" index (or the WinEventLog* sources).
See Configure Computers to Forward and Collect Events (https://msdn.microsoft.com/en-us/library/cc748890(v=ws.11).aspx) for details on how to configure a computer as a collector of logs.
Send any suggestions, questions etc. to support@altairtech.ca.
For up-to-date documentation, see: https://www.eventid.net/splunk_addon.asp
New dashboards related to users and groups creation/deletion, various improvements for Splunk 7.1.x
Added Users and Groups dashboard - monitoring of user and group creation/deletion, Admins group membership changes
Bug fixes and esthetical changes for version 7..1
Existing dashboards improvements
New dashboards: Interesting Processes, XML (provides support for events recorded via renderXML attribute)
Existing dashboards improvements
New dashboards: Interesting Processes, XML (provides support for events recorded via renderXML attribute)
Version 1.2.0 adds support for Windows event logs collected from remote hosts via WMI.
A new section in the Audit provides details on processes of interest. Process audit must be enabled (see the Readme file for details).
Version 1.1.0 bring an improved dashboard with several additional statistics and compatibility with both the logs collected by the Universal Forwarder and the Windows event logs collected locally.
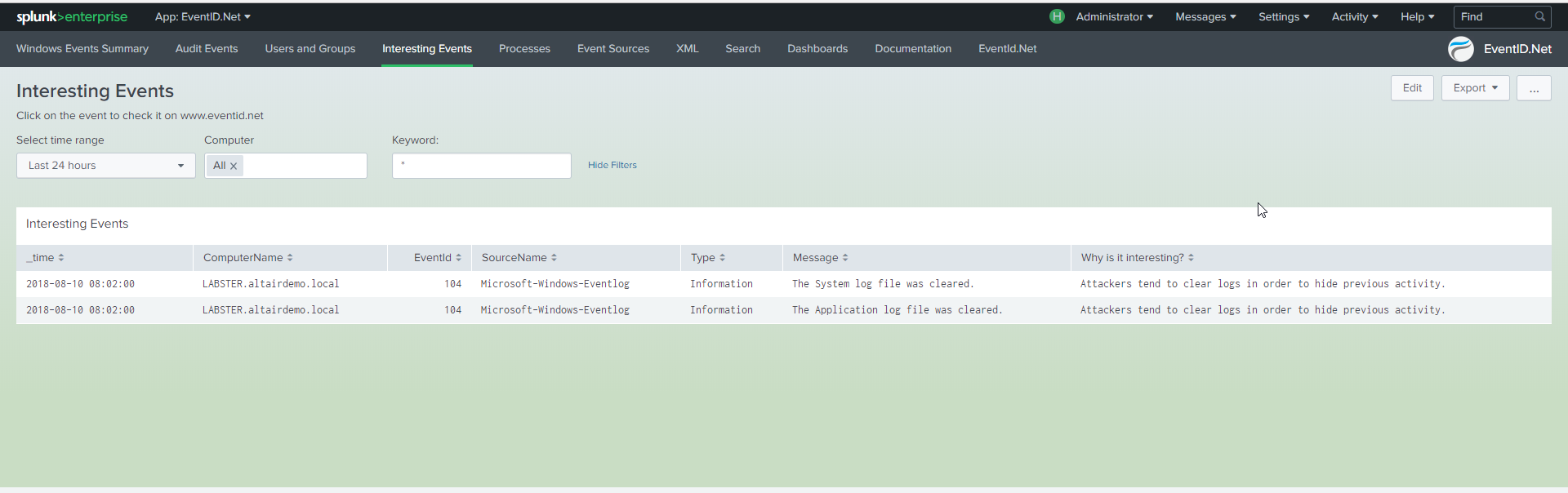
The www.eventid.net Splunk app provides integration between the Windows event logs collected by Splunk via the Universal Forwarder and www.eventid.net. Views for events, event sources and audit events make the administration and troubleshooting of Windows events much easier and intuitive.
As a Splunkbase app developer, you will have access to all Splunk development resources and receive a 10GB license to build an app that will help solve use cases for customers all over the world. Splunkbase has 1000+ apps from Splunk, our partners and our community. Find an app for most any data source and user need, or simply create your own with help from our developer portal.