








Automater Error:
- If you get the following error when running Automater: "External search command 'automater_wrapper"
- Make sure you have python installed and associated with .py files (especially Windows environments)
- Please run the following command: chmod +x /opt/splunk/etc/apps/ForensicInvestigator/bin/Automater.py
- This will be fixed in the next release. Thanks for your patience.
Note: To make the Investigator Chat work for regular users, they must have the admin_all_objects capability assigned. This can be accomplished by creating a role called chat_write and assign that role to the users. Finally assign the admin_all_objects capability to that newly created role.
Installation is very easy. Either download it within Splunk or from this Splunkbase page. Run setup (Help -> Configure App)
Currently the app contains no props or transforms (unless processing MIR output) so there is no risk of it modifying your data.
Stay tuned as we will be adding more tools as they are requested.
| URL/IP | Domain | Files | En/Decoder | Host |
|---|---|---|---|---|
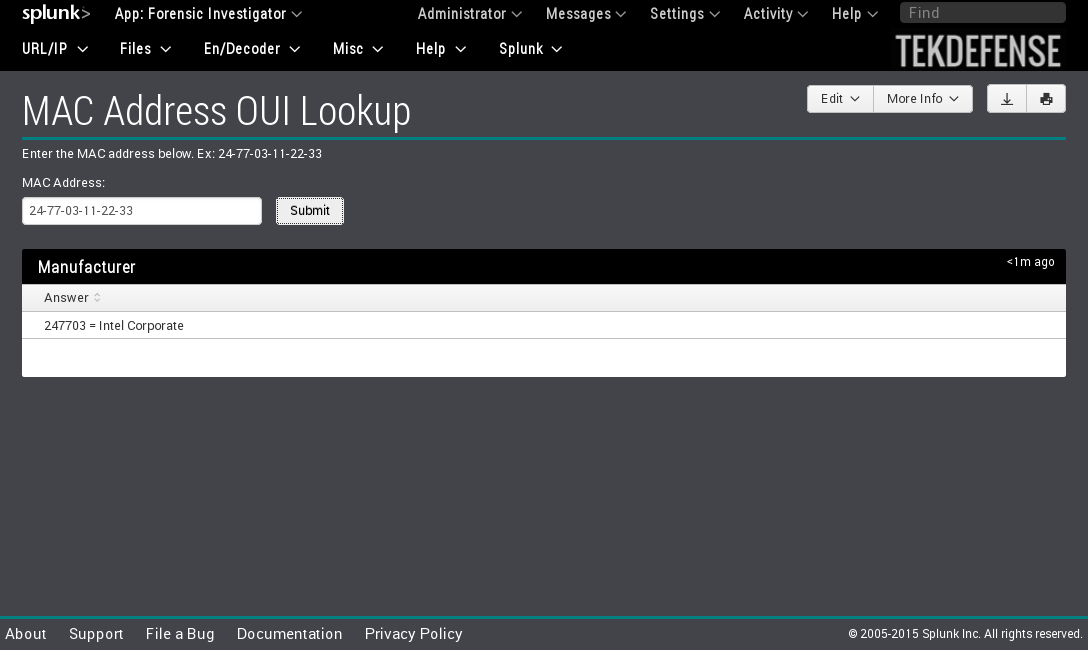
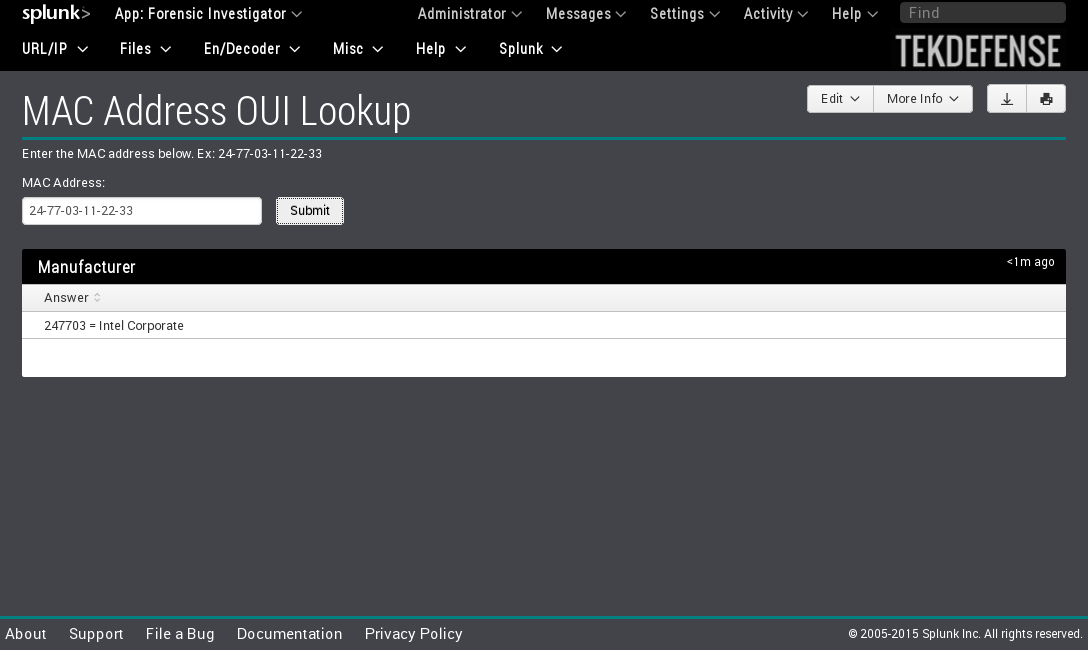
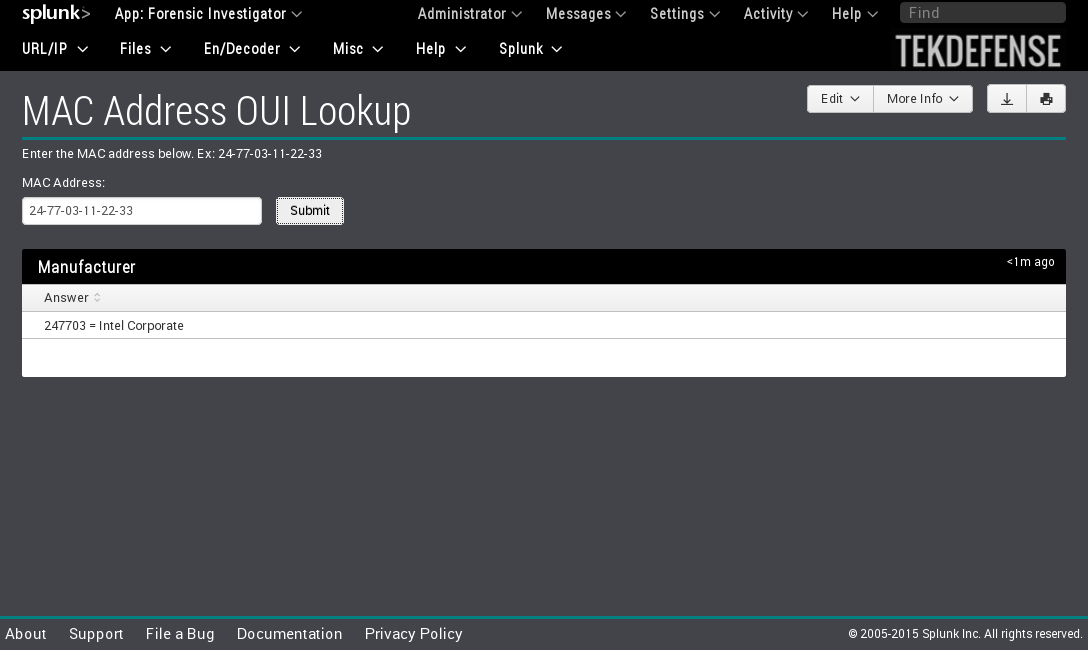
| VT Lookup * | WHOIS Lookup 1 * | VT Lookup * | Cyber Chef | MAC OUI Lookup |
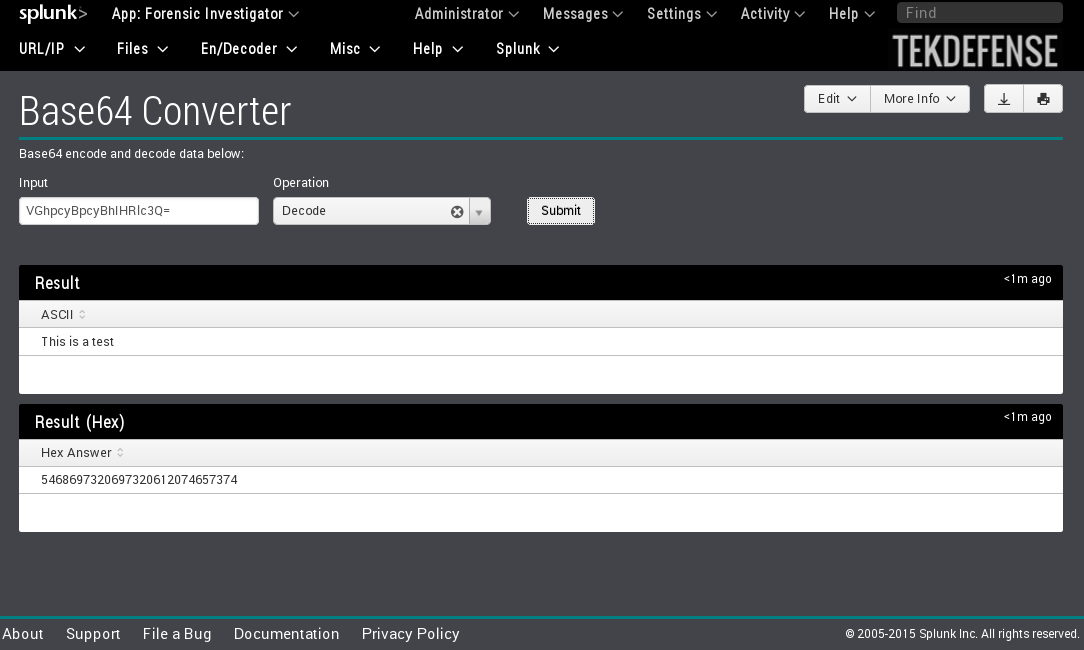
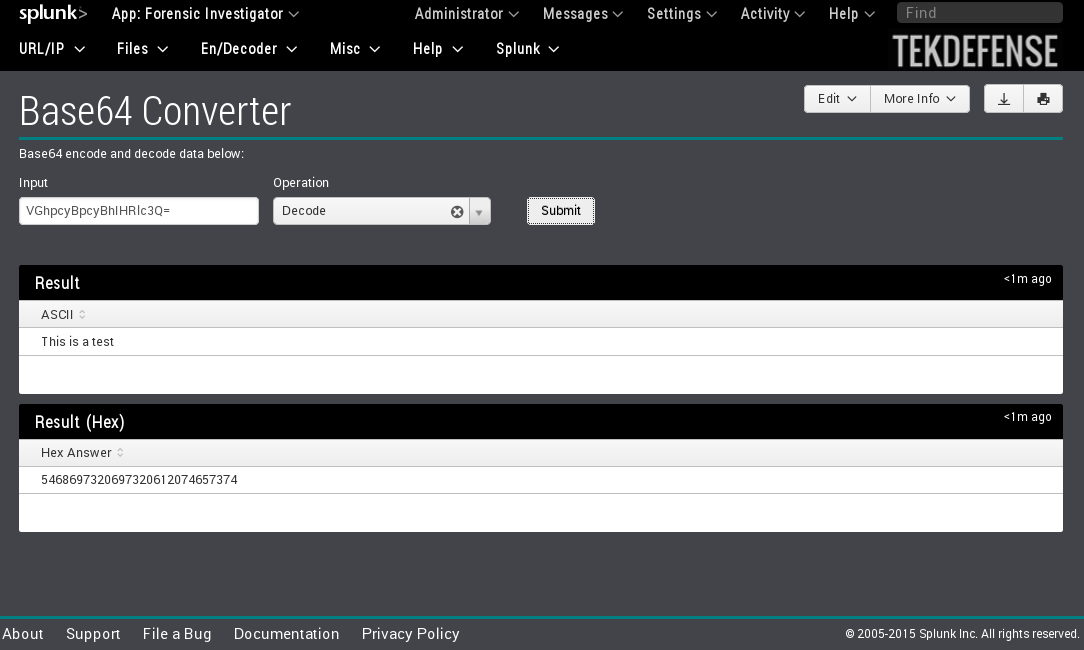
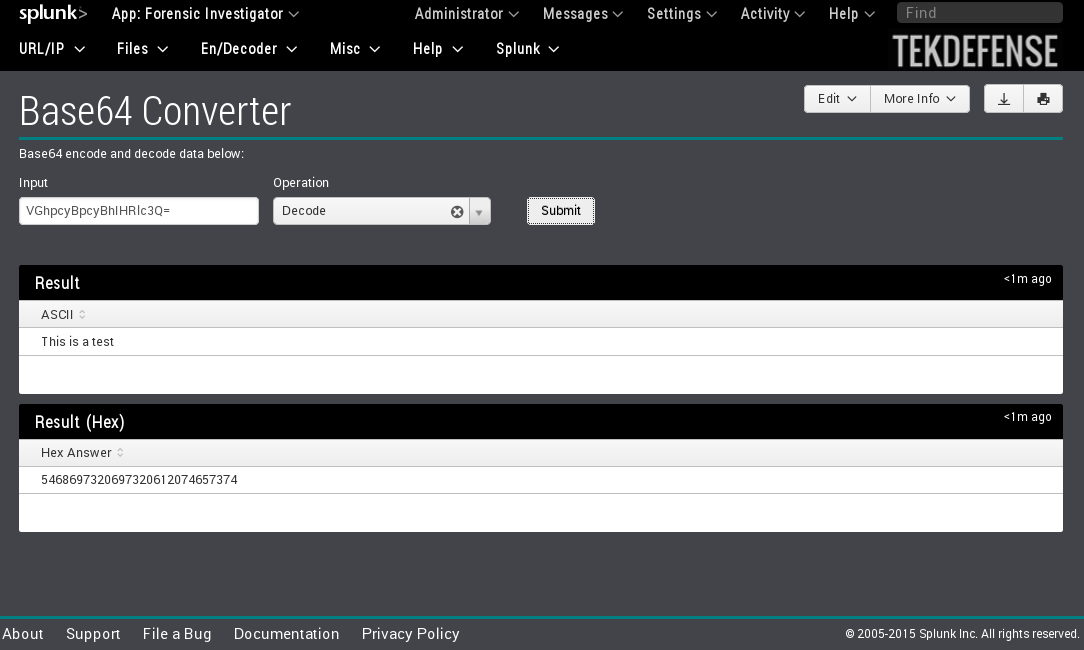
| Automater * | WHOIS Lookup 2 * | Automater * | Base64 Converter | Ping |
| Metascan IP * | Metscan hash * | Hex Converter | Traceroute | |
| URL Unshortener | File Hasher | XOR Converter | SMB Share View | |
| LinkExtractor * | Hash Identifier | NetBios Viewer | ||
| GeoIP Lookup | ROT(n) Converter | Port Scanner | ||
| DNS Resolver | IP Converter | Banner Grabber | ||
| URL Decoder | ||||
| URL Parser |
* Requires Internet access / API calls
vim /etc/samba/smb.conf (add to the bottom of the file)
[monitor]
comment = Watch for incoming files
available = yes
writeable = yes
browseable = yes
public = yes
path = /monitor
guest ok = yes
read only = no
create mask = 0644
directory mask = 0755
force user = mirmonitor
useradd mirmonitor
passwd mirmonitor
<enter password>
smbpasswd –a mirmonitor
<enter password>
Service smbd restart
Service nmbd restart
Drop Redline and MIR xml files in the following directory structure:
/monitor/<host>/<xml-files>
/monitor/TEK1/w32processes.xml
Version 1.1.8
- Added option to hide the MIR menus via the setup screen
- Added proxy support to setup screen
- Made vtLookup proxy aware
- Made vtLookup accept and use non-default API key
- Added CyberChef (En/Decoder -> CyberChef) - Big thanks to GCHQ for the awesome tool!
- Added ePO Connector to control McAfee ePolicy Orchestrator
- Requires editing bin\epoconnector.py and adding ePO IP, port, username, and password
Version 1.1.7
- Added Traceroute (Host -> Traceroute)
- Added Unshortener (URL/IP -> URL Unshortener)
- Added IP Converter (En/Decoder -> IP Converter)
- Added Processing of FireEye/Mandiant MIR output (Check details tab for instructions)
- System
- Network
- Processes
- Services
- Ports
- Tasks
- Prefetch
- ShimCache
- DNS
- User account
- URL History
- Driver Modules
- Persistence
- File
- Eventlog
New Features in v1.1.4
- Updated Investigator Chat 2.0!
- Added Ping tool (Host --> Ping)
- Added SMB Share Viewer (Host --> SMB Share Viewer)
- Added NetBIOS Viewer (Host --> NetBIOS Viewer)
- Added Port scanner (Host --> Port Scanner)
- Added Banner grabber (Host --> Banner grabber)
- Added Bulk searching of data using any field (Toolbox -> Bulk Search - Wild)
- Added Bulk searching of data using a specific field (Toolbox -> Bulk Search - Field)
- Added ASCII Table cheatsheet (Toolbox -> Cheat sheets -> ASCII Table)
- Added Ports and services cheatsheet (Toolbox -> Cheat sheets -> Ports and Services)
- Added subnetting cheatsheet (Toolbox -> Cheat sheets -> Subnetting)
Maintenance in v.1.1.4
- Renamed the xml files to increase simplicity
Version 1.1.3
- Added a chat program for collaboration! It is a first stab, but give it a try (Help -> Chat Program)
- Added an additional whois lookup vendor - api.hackertarget.com - ex: http://api.hackertarget.com/whois/?q=splunk.com
- Added a link extractor to rip links out of a page (URL/IP -> Link Extractor)
- Added permalink information to VT lookup page
- Added disk usage monitor (Help -> Disk Monitor) (Uses REST API)
- Added license analysis page (Help -> License Usage) (*Need to have _internal logs on indexer and role based access)
- Fixed VT lookup script, incorrectly detecting MD5 hashes in URL - if (re.findall(r"(^[a-fA-F\d]{32})", sys.argv[1]))
- Fixed VT Lookup script, removed leading white spaces lstrip()
- Fixed bug in BulkWhois to provide state/province information
Version 1.1.2
- First version of the app that is Splunk certified!
- Removed temporary csv file from package
- Edited python script to clean up temp files
v 1.0.9 - Conforming to app development/certification requirements
- app.conf now has a proper description
- Separated the file hasher stanzas from app.conf and placed them in filehasher.conf
- Created a README file in the install package
- removed local directory
1.0.7
- raw_data properly parsed in whois tool
- Hasher now outputs hashes in caps
- Added File Hasher tool - based on file upload
- Temporarily removed Owner Search - it will be back
1.0.5
- Renamed category headings - parsed based on new tools and future plans
- Added whois lookup
- Added hashing tool - MD5, SHA1, SHA224, SHA256, SHA384, SHA512
- Added hash-identifier.py (Props to Zion3R at Blackploit)
1.0.4
- Updated MAC OUI Lookup to return multiple values based on partial match
- Added Automater!
- CSS updates
- Fixed word wrap for results with no white space
- Added drop shadow on dropdown menu
- Changed dropdown menu text color to teal
1.0.3
- ROT conversion is now case sensitive
- Added Hex panel to Base64
- Added GeoIP lookup for user selected IP
- Added MAC OUI lookup
- DNS lookup - local lookups
Version 1.0.1
- Introduce the apps and tools
As a Splunkbase app developer, you will have access to all Splunk development resources and receive a 10GB license to build an app that will help solve use cases for customers all over the world. Splunkbase has 1000+ apps from Splunk, our partners and our community. Find an app for most any data source and user need, or simply create your own with help from our developer portal.