See here for product details.
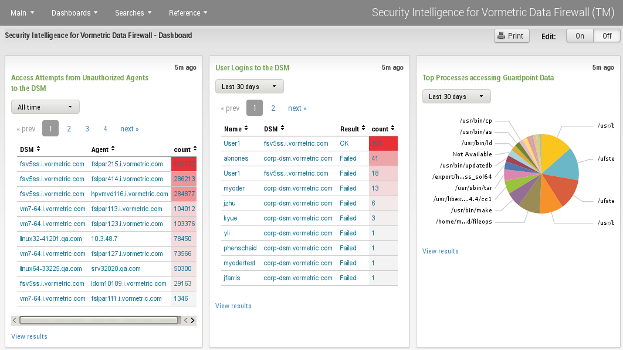
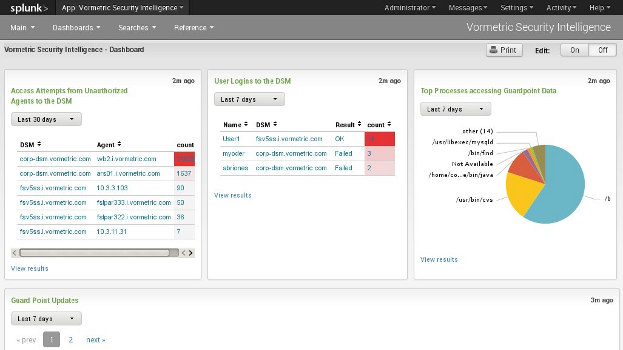
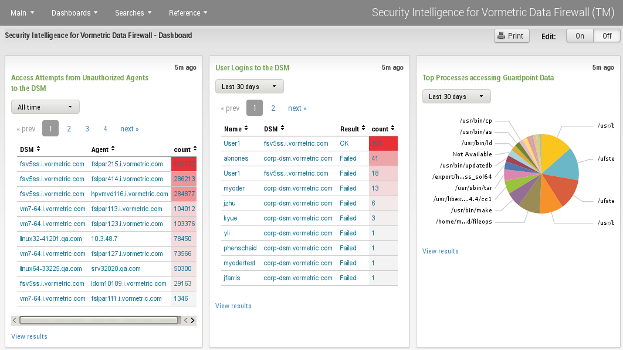
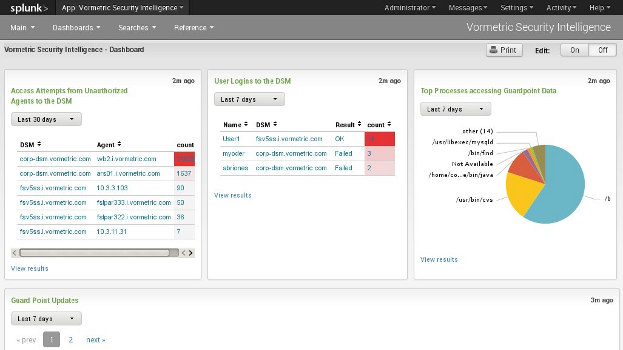
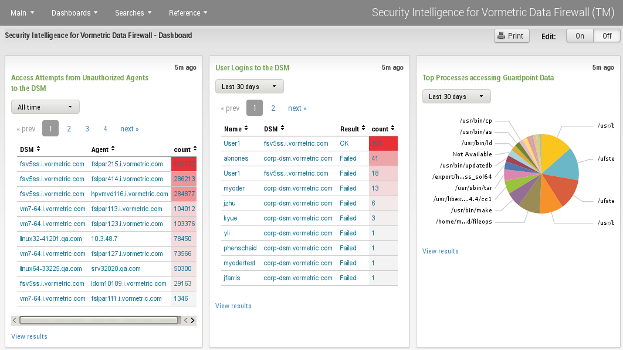
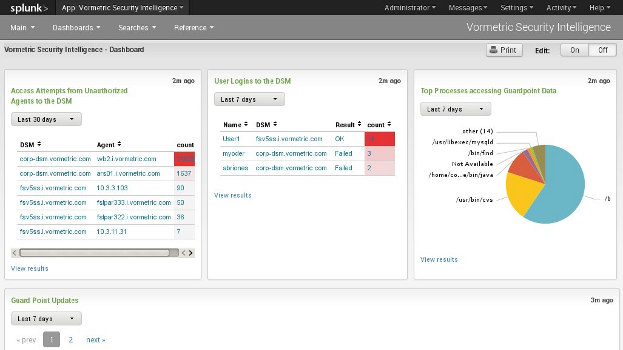
Much of the information required for the reports is extracted from audit log messages generated by Vormetric agents when user programs access files protected by a Guard Point, which is a directory protected by the Vormetric Filesystem agent. This requires that the Guard Point has been set up using a policy where the rules include an audit effect, and that the agent has been configured to send "INFO" level log messages to the Splunk system, either directly from the agent, or forwarded by the DSM.
If info-level audit logging of Guard Point accesses is not provided, the Splunk reports might not provide useful results.
The log streams provided to Splunk must in RFC5424 Syslog format, else field extraction will not work correctly. This is selected in the DSM when defining the syslog stream formats.
The reports and searches might not provide useful information until a sufficient volume of log events has been captured by Splunk.
1.0.14 - updated 3rd October 2018
Updated search strings to include IANA message source ID of 4096 (Thales) as well as 21513 (Vormetric). This is required for VTE release 6.1.2 and later.
Updated to include VTE 6.3 message catalogs
Updated to contain VTE 6.1 and DSM 6.1 error catalogs.
As a Splunkbase app developer, you will have access to all Splunk development resources and receive a 10GB license to build an app that will help solve use cases for customers all over the world. Splunkbase has 1000+ apps from Splunk, our partners and our community. Find an app for most any data source and user need, or simply create your own with help from our developer portal.