
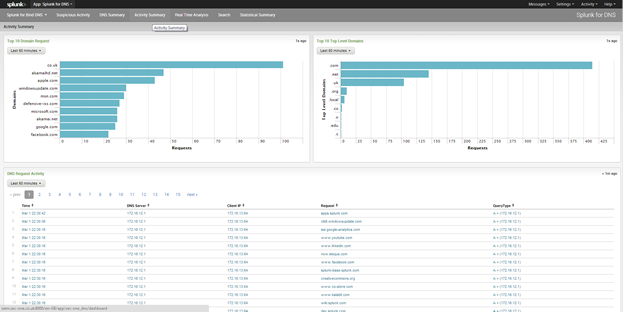


The Splunk for DNS will provide you with a dashboard that will provides you with summary of DNS actives in your network, assuming you have a well-defined DNS infrastructure.

Requirements:
Installation:
The installation guidance is one way to get DNS data into Splunk. You can use other methods, as long as the data source type is set to "syslog".
1. Install the Bind server components on your preferred Linux host
2. Install the Syslog-NG, or your preferred syslog forwarder.( ) on the host Bind server.
3. Configure, see below.
Configuration:
options {
forwarders {
208.67.222.222;
208.67.220.220;
};
querylog yes;
};
zone "." {
type hint;
file "/etc/db.cache";
};
logging{
channel simple_log {
file "/var/log/named/bind.log";
severity debug;
print-category yes;
print-severity yes;
print-time yes;
};
category client {simple_log; };
category queries {simple_log; };
category default {simple_log; };
category security {simple_log; };
};
};
destination splunk {
udp(xxx.xxx.xxx.xxx);#Replace xxx with the IP of your Splunk syslog listener.
};
source named {
file("/var/log/named/bind.log" log_prefix("BIND-DNS"));
};
log {
source(named);
destination(splunk);
};
Correction to the prop.conf file.
As a Splunkbase app developer, you will have access to all Splunk development resources and receive a 10GB license to build an app that will help solve use cases for customers all over the world. Splunkbase has 1000+ apps from Splunk, our partners and our community. Find an app for most any data source and user need, or simply create your own with help from our developer portal.